B.Com-204/ B.Com(H)-206: Fundamentals of Computers
COMPUTER AND ITS
CHARACTERISTICS; ADVANTAGES AND LIMITATIONS
An electronic device which is
capable of receiving information (data) in a particular form and of performing
a sequence of operations in accordance with a predetermined but variable set of
procedural instructions (program) to produce a result in the form of
information or signals.
A computer generally means a
programmable machine. The two principal characteristics of a computer are: it
responds to a specific set of instructions in a well-defined manner and it can
execute a pre-recorded list of instructions (a program).
A computer is a device that
accepts information (in the form of digitalized data) and manipulates it for
some result based on a program or sequence of instructions on how the data is
to be processed.
Characteristics
of a computer
1.
Speed: As you know
computer can work very fast. It takes only few seconds for calculations that we
take hours to complete. You will be surprised to know that computer can perform
millions (1,000,000) of instructions and even more per second. Therefore, we
determine the speed of computer in terms of microsecond (10-6 part of a second)
or nanosecond (10 to the power -9 part of a second). From this you can imagine
how fast your computer performs work.
In
general, no human being can compete to solving the complex computation, faster
than computer.
2.
Accuracy: The degree of
accuracy of computer is very high and every calculation is performed with the
same accuracy. The accuracy level is 7 determined on the basis of design of
computer. The errors in computer are due to human and inaccurate data. Since
Computer is programmed, so whatever input we give it gives result with
accurately. In addition to being fast, computers are also accurate. Errors that
may occur can almost always be attributed to human error (inaccurate data,
poorly designed system or faulty instructions/programs written by the
programmer)
3.
Diligence: A computer is
free from tiredness, lack of concentration, fatigue, etc. It can work for hours
without creating any error. If millions of calculations are to be performed, a
computer will perform every calculation with the same accuracy. Due to this
capability it overpowers human being in routine type of work.
Computer
can work for hours without any break and creating error. Unlike human beings,
computers are highly consistent. They do not suffer from human traits of
boredom and tiredness resulting in lack of concentration. Computers, therefore,
are better than human beings in performing voluminous and repetitive jobs.
4.
Versatility: It means the
capacity to perform completely different type of work. You may use your
computer to prepare payroll slips. Next moment you may use it for inventory
management or to prepare electric bills.
Computers
are versatile machines and are capable of performing any task as long as it can
be broken down into a series of logical steps. The presence of computers can be
seen in almost every sphere – Railway/Air reservation, Banks, Hotels, Weather
forecasting and many more.
5. Power of
Remembering:
Computer has the power of storing any amount of information or data. Any
information can be stored and recalled as long as you require it, for any
numbers of years. It depends entirely upon you how much data you want to store
in a computer and when to lose or retrieve these data. It can remember data for
us.
6.
No IQ: Computer is a
dumb machine and it cannot do any work without instruction from the user. It
performs the instructions at tremendous speed and with accuracy. It is you to
decide what you want to do and in what sequence. So a computer cannot take its
own decision as you can. Computer does not work without instruction.
7.
Feelings: A computer does
not have feelings or emotions, taste, knowledge and experience. Thus, it does
not get tired even after long hours of work. It does not distinguish between
users.
8.
Storage: The Computer
has an in-built memory where it can store a large amount of data. You can also
store data in secondary storage devices such as floppies, which can be kept
outside your computer and can be carried to other computers. Today’s computers
can store large volumes of data. A piece of information once recorded (or
stored) in the computer can never be forgotten and can be retrieved almost
instantaneously.
Advantages
of using computers
Benefits from using computers are
possible because computers have the advantages of speed, reliability,
consistency, storage, and communications.
1.
Speed: When data,
instructions, and information flow along electronic circuits in a computer,
they travel at incredibly fast speeds. Many computers process billions or
trillions of operations in a single second. Processing involves computing
(e.g., adding, subtracting), sorting (e.g., alphabetizing), organizing,
displaying images, recording audio, playing music, and showing a movie or
video.
2.
Reliability: The electronic
components in modern computers are dependable and reliable because they rarely
break or fail.
3.
Consistency: Given the same
input and processes, a computer will produce the same results — consistently. A
computing phrase — known as garbage in, garbage out — points out that the
accuracy of a computer’s output depends on the accuracy of the input. For
example, if you do not use the flash on a digital camera when indoors, the
resulting pictures that are displayed on the computer screen may be unusable
because they are too dark.
4.
Storage: A computer can
transfer data quickly from storage to memory, process it, and then store it
again for future use. Many computers store enormous amounts of data and make
this data available for processing anytime it is needed.
5.
Communications: Most computers
today can communicate with other computers, often wirelessly. Computers with
this capability can share any of the four information processing cycle
operations — input, process, output, and storage — with another computer or a
user.
Disadvantages
(limitations) of using computers
Some disadvantages of computers
relate to health risks, the violation of privacy, public safety, the impact on
the labour force, and the impact on the environment.
1.
Health Risks: Prolonged or
improper computer use can lead to injuries or disorders of the hands, wrists,
elbows, eyes, neck, and back. Computer addiction occurs when someone becomes
obsessed with using a computer. Individuals suffering from technology overload
feel distressed when deprived of computers and mobile devices. Once recognized,
both computer addiction and technology overload are treatable disorders.
2.
Violation of
Privacy:
Nearly every life event is stored in a computer somewhere - in medical records,
credit reports, tax records, etc. In many instances, where personal and
confidential records were not protected properly, individuals have found their
privacy violated and identities stolen.
3.
Public Safety: Adults, teens,
and children around the world are using computers to share publicly their
photos, videos, journals, music, and other personal information. Some of these
unsuspecting, innocent computer users have fallen victim to crimes committed by
dangerous strangers.
4.
Impact on Labour
Force:
Although computers have improved productivity in many ways and created an
entire industry with hundreds of thousands of new jobs, the skills of millions
of employees have been replaced by computers. Thus, it is crucial that workers
keep their education up-to-date. A separate impact on the labour force is that
some companies are outsourcing jobs to foreign countries instead of keeping
their homeland labour force employed.
5.
Impact on
Environment:
Computer manufacturing processes and computer waste are depleting natural
resources and polluting the environment. When computers are discarded in
landfills, they can release toxic materials and potentially dangerous levels of
lead, mercury, and flame retardants.
FUNCTIONAL COMPONENTS OF A
COMPUTER SYSTEM
Computer systems ranging from a
controller in a microwave oven to a large supercomputer contain components
providing five functions. A typical personal computer has hard, floppy and
CD-ROM disks for storage, memory and CPU chips inside the system unit, a
keyboard and mouse for input, and a display, printer and speakers for output.
The arrows represent the direction information flows between the functional
units. A computer can process data, pictures, sound and graphics. They can
solve highly complicated problems quickly and accurately. A computer performs
basically five major computer operations or functions irrespective of their
size and make. These are:
1.
It accepts data
or instructions by way of input,
2.
It stores data,
3.
It can process
data as required by the user,
4.
It gives results
in the form of output,
5. It controls all operations inside a computer.
1. Input: This is the process of entering data
and programs in to the computer system. You should know that computer is an
electronic machine like any other machine which takes as inputs raw data and
performs some processing giving out processed data. Therefore, the input unit
takes data from us to the computer in an organized manner for processing.
2.
Storage: The process of
saving data and instructions permanently is known as storage. Data has to be
fed into the system before the actual processing starts. It is because the
processing speed of Central Processing Unit (CPU) is so fast that the data has
to be provided to CPU with the same speed. Therefore the data is first stored
in the storage unit for faster access and processing. This storage unit or the
primary storage of the computer system is designed to do the above
functionality. It provides space for storing data and instructions. The storage
unit performs the following major functions:
1)
All data and
instructions are stored here before and after processing.
2) Intermediate results of processing are also stored
here.
3.
Processing: The task of
performing operations like arithmetic and logical operations is called
processing. The Central Processing Unit (CPU) takes data and instructions from
the storage unit and makes all sorts of calculations based on the instructions
given and the type of data provided. It is then sent back to the storage unit.
4.
Output: This is the
process of producing results from the data for getting useful information.
Similarly the output produced by the computer after processing must also be
kept somewhere inside the computer before being given to you in human readable
form. Again the output is also stored inside the computer for further
processing.
5.
Control: The manner how
instructions are executed and the above operations are performed. Controlling
of all operations like input, processing and output are performed by control
unit. It takes care of step by step processing of all operations inside the
computer.
Functional Units
In order to carry out the operations
mentioned in the previous section the computer allocates the task between its
various functional units. The computer system is divided into three separate
units for its operation. They are:
1.
Arithmetic
Logical Unit (ALU):
After you enter data through the input device it is stored in the primary
storage unit. The actual processing of the data and instruction are performed
by Arithmetic Logical Unit. The major operations performed by the ALU are
addition, subtraction, multiplication, division, logic and comparison. Data is
transferred to ALU from storage unit when required. After processing the output
is returned back to storage unit for further processing or getting stored.
2.
Control Unit
(CU):
The next component of computer is the Control Unit, which acts like the
supervisor seeing that things are done in proper fashion. Control Unit is
responsible for co-ordinating various operations using time signal. The control
unit determines the sequence in which computer programs and instructions are
executed. Things like processing of programs stored in the main memory,
interpretation of the instructions and issuing of signals for other units of
the computer to execute them. It also acts as a switch board operator when
several users access the computer simultaneously. Thereby it coordinates the
activities of computer’s peripheral equipment as they perform the input and
output.
3.
Central
Processing Unit (CPU): The ALU and the CU of a computer system are jointly
known as the central processing unit. You may call CPU as the brain of any
computer system. It is just like brain that takes all major decisions, makes
all sorts of calculations and directs different parts of the computer functions
by activating and controlling the operations.
TYPES OF MEMORY & MEMORY HIERARCHY; CLASSIFICATION OF COMPUTERS
RAM
- Random Access Memory: RAM is the main memory of a computer. Main memory is
used to store all of the working information of the computer such as the
operating system, user programs and data. Main memory should not be confused
with hard disk space which is used to permanently store data. RAM is volatile.
The contents of RAM are lost when the computer is switched off.
DRAM
- Dynamic RAM: Dynamic
RAM is the most common type of RAM used in computers. It is relatively easy to
manufacture and so is cheap. However, DRAM contents must be continually
refreshed. The process of refreshing the memory takes time and while the memory
is being refreshed it cannot be read from or written to. This makes DRAM cheap
but slow. DRAM is cheap but slow and is used for main memory.
ROM
- Read Only Memory: Whereas
RAM is volatile, ROM is non-volatile which is to say that the contents are not
lost when power is removed. ROM chips come with instructions already burned
into the chip. It is commonly used for computer BIOS chips. ROM is cheap in
high quantities and is generally used for PC BIOSes.
PROM - Programmable ROM: PROM chips do
not lose their data when power is removed but, unlike standard ROM chips, come
without a program already installed. The programs for the PROM chips can be
'burned' into them with a special piece of programming hardware. Once burned
this way the contents are never lost but nor can they be altered. PROM chips
are commonly used where engaging a chip foundry to manufacture a custom ROM
chip would be too expensive. PROM is expensive and is used for low volume
applications.
EPROM
- Erasable Programmable ROM: EPROM chips can be erased once
programmed, thus making them ideal for testing new applications where a ROM
chip will be required. They can be easily recognised by the plastic 'window' on
the top of the chip. This is used to erase the contents of the chip by shining
ultra-violet light onto it. EPROMs are expensive but reusable and are used for
testing.
Types
of Memory and Memory Hierarchy
Although memory is technically
any form of electronic storage, it is used most often to identify fast,
temporary forms of storage. If your computer's CPU had to constantly access the
hard drive to retrieve every piece of data it needs, it would operate very
slowly. When the information is kept in memory, the CPU can access it much more
quickly. Most forms of memory are intended to store data temporarily.
In the diagram given below, the
CPU accesses memory according to a distinct hierarchy. Whether, it comes from
permanent storage (the hard drive) or input (the keyboard), most data goes in
random access memory (RAM) first. The CPU then stores pieces of data it will
need to access, often in a cache, and maintains certain special instructions in
the register.
All of the components in your
computer, such as the CPU, the hard drive and the operating system, work
together as a team, and memory is one of the most essential parts of this team.
From the moment you turn your computer on until the time you shut it down, your
CPU is constantly using memory.
A typical computer has:
§
Level
1 and level 2 caches
§
Normal
system RAM
§
Virtual
memory
§
A
hard disk
Cache
and Registers
‘Caches’ are designed to
lessen this bottleneck by making the data used most often by the CPU instantly
available. This is accomplished by building a small amount of memory, known as
primary or level 1 cache, right into the CPU. Level 1 cache is very small, normally
ranging between 2 kilobytes (KB) and 64 KB.
The secondary or level 2 cache
typically resides on a memory card located near the CPU. The level 2 cache has
a direct connection to the CPU. A dedicated integrated circuit on the
motherboard, the L2 controller, regulates the use of the level 2 cache by the
CPU. Depending on the CPU, the size of the level 2 cache ranges from 256 KB to
2 megabytes (MB). In most systems, data needed by the CPU is accessed from the
cache approximately 95 percent of the time, greatly reducing the overhead
needed when the CPU has to wait for data from the main memory.
Some inexpensive systems dispense
with the level 2 cache altogether. Many high performance CPUs now have the
level 2 cache actually built into the CPU chip itself. Therefore, the size of
the level 2 cache and whether it is onboard (on the CPU) is a major determining
factor in the performance of a CPU.
A particular type of RAM, static
random access memory (SRAM), is used primarily for cache. SRAM uses multiple
transistors, typically four to six, for each memory cell. It has an external
gate array known as a bi-stable multi-vibrator that switches, or flip-flops,
between two states. This means that it does not have to be continually
refreshed like DRAM. Each cell will maintain its data as long as it has power.
Without the need for constant refreshing, SRAM can operate extremely quickly.
But the complexity of each cell makes it prohibitively expensive for use as
standard RAM.
The SRAM in the cache can be
asynchronous or synchronous. Synchronous SRAM is designed to exactly match the
speed of the CPU, while asynchronous is not. That little bit of timing makes a
difference in performance. Matching the CPU's clock speed is a good thing, so
always look for synchronized SRAM.
The final step in memory is the ‘Registers’. These are memory cells built
right into the CPU that contain specific data needed by the CPU, particularly
the arithmetic and logic unit (ALU). An integral part of the CPU itself, they
are controlled directly by the compiler that sends information for the CPU to
process.
Computer
Classification: By Size and Power
Computers can be generally
classified by size and power as follows, though there is considerable overlap:
§
Personal
computer:
A small, single-user computer based on a microprocessor. In addition to the
microprocessor, a personal computer has a keyboard for entering data, a monitor
for displaying information, and a storage device for saving data.
§
Workstation: A powerful,
single-user computer. A workstation is like a personal computer, but it has a
more powerful microprocessor and a higher-quality monitor.
§
Minicomputer: A multi-user
computer capable of supporting from 10 to hundreds of users simultaneously.
§
Mainframe: A powerful
multi-user computer capable of supporting many hundreds or thousands of users
simultaneously.
§
Supercomputer: an extremely
fast computer that can perform hundreds of millions of instructions per second.
A PC can be defined as a small,
relatively inexpensive computer designed for an individual user. PCs are based
on the microprocessor technology that enables manufacturers to put an entire
CPU on one chip. Businesses use personal computers for word processing,
accounting, desktop publishing, and for running spreadsheet and database
management applications. At home, the most popular use for personal computers
is for playing games and surfing the Internet.
Although personal
computers are designed as single-user systems, these systems are normally
linked together to form a network. In terms of power, nowadays high-end models
of the Macintosh and PC offer the same computing power and graphics capability
as low-end workstations by Sun Microsystems, Hewlett-Packard, and DELL.
Workstation
Workstation is a computer used for
engineering applications (CAD/CAM), desktop publishing, software development,
and other such types of applications, which require a moderate amount of
computing power and relatively high quality graphics capabilities.
Minicomputer
Mainframe
Mainframe is a very
large in size and an expensive computer capable of supporting hundreds, or even
thousands, of users simultaneously. Mainframe executes many programs
concurrently. Mainframes support many simultaneous programs execution.
Supercomputer
Sr. No.
|
Type
|
Specifications
|
1
|
Personal Computer (PC)
|
Single user computer system. Moderately powerful microprocessor.
|
2
|
WorkStation
|
Single user computer system. Similar to Personal Computer but have
more powerful microprocessor.
|
3
|
Mini Computer
|
Multi-user computer system. Capable of supporting hundreds of users
simultaneously.
|
4
|
Main Frame
|
Multi-user computer system. Capable of supporting hundreds of users
simultaneously. Software technology is different from minicomputer.
|
5
|
Supercomputer
|
An extremely fast computer, which can perform hundreds of millions of
instructions per second.
|
INPUT DEVICES
An input device is any hardware
device that sends data to a computer, allowing you to interact with and control
the computer. It allows you to enter information. The most fundamental pieces
of information are keystrokes on a keyboard and clicks with a mouse. These two
input devices are essential for you to interact with your computer. Many other
input devices exist for entering other types of information, such as images,
audio and video.
Following are few of
the important input devices, which are used in Computer Systems:
- Keyboard
- Mouse
- Joystick
- Light pen
- Track Ball
- Scanner
- Graphic Tablet
- Microphone
- Magnetic Ink Card Reader (MICR)
- Optical Character Reader
(OCR)
- Bar Code Reader
- Optical Mark Reader
Keyboard
S. No.
|
Keys
|
Description
|
1
|
Typing Keys
|
These keys include the letter keys (A-Z) and digits keys (0-9) which
generally give same layout as that of typewriters.
|
2
|
Numeric Keypad
|
It is used to enter numeric data or cursor movement. Generally, it
consists of a set of 17 keys that are laid out in the same configuration used
by most adding machine and calculators.
|
3
|
Function Keys
|
The twelve functions keys are present on the keyboard. These are
arranged in a row along the top of the keyboard. Each function key has unique
meaning and is used for some specific purpose.
|
4
|
Control keys
|
These keys provide cursor and screen control. It includes four
directional arrow key. Control keys also include Home, End, Insert, Delete,
Page Up, Page Down, Control(Ctrl), Alternate(Alt), Escape(Esc).
|
5
|
Special Purpose
Keys
|
Keyboard also contains some special purpose keys such as Enter, Shift,
Caps Lock, Num Lock, Space bar, Tab, and Print Screen.
|
Mouse
Mouse is most popular Pointing device.
It is a very famous cursor-control device. It is a small palm size box with a
round ball at its base which senses the movement of mouse and sends
corresponding signals to CPU on pressing the buttons. Generally, it has two
buttons called left and right button and scroll bar is present at the mid.
Mouse can be used to control the position of cursor on screen, but it cannot be
used to enter text into the computer.
Advantages
·
Easy to use
·
Not very expensive
·
Moves the cursor faster than the arrow keys of keyboard.
Joystick is also a pointing device,
which is used to move cursor position on a monitor screen. It is a stick having
a spherical ball at its both lower and upper ends. The lower spherical ball
moves in a socket. The joystick can be moved in all four directions. The
function of joystick is similar to that of a mouse. It is mainly used in
Computer Aided Designing (CAD) and playing computer games.
Light pen is a pointing device, which
is similar to a pen. It is used to select a displayed menu item or draw
pictures on the monitor screen. It consists of a photocell and an optical
system placed in a small tube. When light pen's tip is moved over the monitor
screen and pen button is pressed, its photocell sensing element detects the
screen location and sends the corresponding signal to the CPU.
Track Ball
Scanner is an input device, which works
more like a photocopy machine. It is used when some information is available on
a paper and it is to be transferred to the hard disc of the computer for
further manipulation. Scanner captures images from the source which are then
converted into the digital form that can be stored on the disc. These images
can be edited before they are printed.
Digitizer
Digitizer is also
known as Tablet or Graphics Tablet because it converts graphics and pictorial
data into binary inputs. A graphic tablet as digitizer is used for doing fine
works of drawing and images manipulation applications.
Microphone is an
input device to input sound that is then stored in digital form. The microphone
is used for various applications like adding sound to a multimedia presentation
or for mixing music.
Magnetic Ink Card Reader (MICR)
OCR is an input
device used to read a printed text. OCR scans text optically character by
character, converts them into a machine readable code and
stores the text on the system memory.
Bar Code Readers
OMR is a special type of optical
scanner used to recognize the type of mark made by pen or pencil. It is used
where one out of a few alternatives is to be selected and marked. It is
specially used for checking the answer sheets of examinations having multiple
choice questions.
OUTPUT DEVICES
An output device is any
peripheral that receives data from a computer, usually for display, projection,
or physical reproduction. Any device used to send data from a computer to
another device or user is an output device. An output device refers to
user-computer communication devices and devices used for communication between
computers, devices and other peripherals.
Following are few of the important
output devices, which are used in Computer Systems:
·
Monitors
·
Graphic Plotter
·
Printer
Monitors
Monitor commonly called as Visual
Display Unit (VDU) is the main output device of a computer. It forms images
from tiny dots, called pixels that are arranged in a rectangular form. The
sharpness of the image depends upon the number of the pixels.
There are two kinds of viewing screen
used for monitors:
·
Cathode-Ray Tube (CRT)
·
Flat-Panel Display
Cathode-Ray Tube
(CRT) Monitor
A finite number of characters can be
displayed on a screen at once. The screen can be divided into a series of
character boxes - fixed location on the screen where a standard character can
be placed.
Most screens are capable of displaying
80 characters of data horizontally and 25 lines vertically. There are some
disadvantages of CRT:
·
Large in Size
·
High power consumption
Flat-Panel Display
Monitor
The flat-panel display refers to a
class of video devices that have reduced volume, weight and power requirement
compared to the CRT. You can hang them on walls or wear them on your wrists.
Current uses for flat-panel displays include calculators, video games,
monitors, laptop computer, graphics display.
The flat-panel displays are divided
into two categories:
·
Emissive Displays - The emissive displays are
devices that convert electrical energy into light. Examples are plasma panel
and LED (Light-Emitting Diodes).
· Non-Emissive Displays - The
Non-emissive displays use optical effects to convert sunlight or light from
some other source into graphics patterns. Example is LCD (Liquid-Crystal
Device)
Printers
Printer is the most important output
device, which is used to print information on paper.
There are two types of printers:
·
Impact Printers
·
Non-Impact Printers
Impact Printers
The printers that print the characters
by striking against the ribbon and onto the paper are called impact printers.
Characteristics of Impact Printers are
the following:
·
Very low consumable costs
·
Impact printers are very noisy
·
Useful for bulk printing due to low cost
·
There is physical contact with the paper to produce an image
These printers are of two types:
·
Character printers
·
Line printers
Character Printers:
Character Printers are printers, which
print one character at a time.
These are of further two types:
·
Dot Matrix Printer (DMP)
·
Daisy Wheel
Dot Matrix Printer
In the market, one of the most popular
printers is Dot Matrix Printer because of their ease of printing features and
economical price. Each character printed is in form of pattern of Dot's and
head consists of a Matrix of Pins of size (5*7, 7*9, 9*7 or 9*9) which comes
out to form a character that is why it is called Dot Matrix Printer.
·
Inexpensive
·
Widely Used
·
Other language characters can be printed
Disadvantages
·
Slow Speed
· Poor Quality
Daisy Wheel
Head is lying on a wheel and Pins
corresponding to characters are like petals of Daisy (flower name) that is why
it is called Daisy Wheel Printer. These printers are generally used for
word-processing in offices which require a few letters to be sent here and
there with very nice quality representation.
Advantages
·
More reliable than DMP's
·
Better quality
·
The fonts of character can be easily changed.
Disadvantages
·
Slower than DMP's
·
Noisy
· More expensive than
DMP's
Line printers are printers, which print
one line at a time.
These are of further two types:
·
Drum Printer
· Chain Printer
Drum Printer
This printer is like a drum in shape so
it called drum printer. The surface of drum is divided into number of tracks.
Total tracks are equal to size of paper, i.e., for a paper width of 132
characters, Drum will have 132 tracks. A character set is embossed on track.
The different character sets available in market are 48 character set, 64 and
96 characters set. One rotation of drum prints one line. Drum Printers are fast
in speed and prints between 300 to 2000 lines per minute.
Advantages
·
Very high speed
Disadvantages
·
Very expensive
·
Characters fonts cannot be changed
Chain Printer
In this printer, a chain of character
sets are used so it called Chain Printers. A standard character set may have
48, 64, 96 characters.
Advantages
·
Character fonts can easily be changed.
·
Different languages can be used with the same printer.
Disadvantages
·
Noisy
· Do not have the
ability to print any shape of characters.
Non-impact Printers
The printers that print the characters
without striking against the ribbon and onto the paper are called Non-impact
Printers. These printers print a complete page at a time, also called as Page
Printers.
These printers are of two types:
·
Laser Printers
·
Inkjet Printers
Characteristics of Non-impact Printers:
·
Faster than impact printers.
·
They are not noisy.
·
High quality.
· Support many fonts
and different character size.
Laser Printers
Advantages
·
Very high speed.
·
Very high quality output.
·
Gives good graphics quality.
·
Supports many fonts and different character sizes.
Disadvantage
·
Expensive.
· Cannot be used to
produce multiple copies of a document in a single printing.
Inkjet Printers
Inkjet printers are non-impact
character printers based on a relatively new technology. They print characters
by spraying small drops of ink onto paper. Inkjet printers produce high quality
output with presentable features.
Advantages
·
High quality printing
·
More reliable
Disadvantages
·
Expensive as cost per page is high
· Slow as compared to
laser printer
MICROSOFT OFFICE; HEADERS AND
FOOTERS
Microsoft
Office is an office suite of desktop applications, servers and services for the
Microsoft Windows, announced by Bill Gates of Microsoft on August 1, 1989 at
COMDEX in Las Vegas. The first version of Office, which was initially a
marketing term for a bundled set of applications contained Microsoft Word,
Microsoft Excel and Microsoft PowerPoint. Over the years, Office applications
have grown substantially closer with shared features such as a common spell
checker and Visual Basic for Applications scripting language. Microsoft also
positions Office as a development platform for line-of-business software under
the Office Business Applications brand. Office is reported to now be used by
over a billion people worldwide.
A
version of Office called Microsoft Office Mobile is available for Android
phones, iPhone and Windows Phone.
Inserting Headers and
Footers:
1. Choose
Header and Footer from the Insert menu.
2. The
Header editing window and the Header and Footer toolbar will appear.
3. Type
the text for the header or footer (the text in a header or footer is formatted
like any other text).
You
can insert page numbers, the document's filename and path, and other codes into
headers and footers (there are a number of options on the Header and Footer
toolbar). The ‘Go to Header’ / ‘Go to Footer’ buttons on the toolbar toggles
the editing window between the header and the footer. The commands to control
headers and footers are on the Design tab which is visible under ‘Header and
Footer Tools’:
*
Set
the header and footer margins on the Position tab.
*
Set
the other options on the Options tab (different first page and odd and even).
If you select either of the options on the Options tab, then you can format the
various headers individually and do things like remove the first page number,
"mirror" the page numbers, etc. Headers and footers can be further controlled
by formatting your document into multiple sections.
MS WORD;
APPLICABILITY OF MS WORD IN TODAY’S CONTEXT
Microsoft Word is word processing software that
allows users to create and edit text documents. Users can start with blank
documents or work from pre-configured templates for projects with frequently
used formats. Microsoft Word is often packaged with the Microsoft Office Suite,
but it is also sold independently.
Microsoft Word let users format various aspects
of a document, ranging from text alignment to custom table layouts. Beyond
basic data entry, the program enables users to insert and format images and
shapes or view and edit PDF files. To simply use the program as a document
viewer, individuals can access documents in Read mode to avoid accidental changes.
The software is valuable for businesses because it allows remote collaboration
on documents projects, making it easy to share file updates.
Microsoft Word is an essential tool for any
individual in today’s digital age. Whether you are a working professional, a
diligent student or an active retiree, proficiency in Microsoft Word is a vital
skill1 that is useful for both complex business requirements as well as basic
day-to-day purposes. Not only is Microsoft Word a flexible tool that allows you
to achieve many of your digital document needs, it is also one of the most
user- friendly applications from the Microsoft Office suite.
1. Smart
Art: The Office 2007 and Office
2010 applications share very similar features for working with a range of
graphics including pictures, Clip Art, Shapes, diagrams and Charts. It’s easy
to confuse SmartArt with the similarly named WordArt. Where WordArt just allows
you to display text using a wide variety of different formats and effects,
SmartArt is a comprehensive and flexible business diagram tool that greatly
improves upon the ‘Diagram Gallery’ feature found in previous versions of
Office. The great thing about SmartArt is the ability to swap between different
diagrams, even diagrams from other categories, without losing the information
that you have already entered. From the selection available, use whichever
SmartArt is appropriate to give your document that little bit extra charm.
2. Turn
Data into Visual Charts: Charts
are created using the same chart ‘engine’ that Excel uses. Accordingly, as your
chart is created, another window will appear containing the Excel-generated
data that the chart is based on. Use the Insert Chart button in the
Illustrations group to insert a chart and select from the variety of options. The
charts are versatile, just like the user-friendly data represented separately
in MS Excel to smooth out the whole data-input-to-graph process.
3. Make
Your Document Interactive: Where
possible, insert hyperlinks on images and text to make your document interactive
(by right clicking on the text/image and clicking hyperlink, you can then
select where you wish to direct the user to). Useful especially when sending
the document online, hyperlinks allow recipients who have opened the file to
click on images/text to directly access relevant web pages or other online
sources of interest.
4.
Watermarks: If
you’re sending an important document or draft sample, you want to be able to
protect your content without having to edit much of it. Insert a watermark
specific to your objectives via the page layout button. You can also customize
your own watermark, and also insert your own picture. This feature is great for
inserting your brand logo in reports or any other official document.
5. Mail
Merge: This feature allows you to
send out bulk emails with unique, customizable elements. For example, you can produce a series of
labels or envelopes for a large mailing list, an email or letter that includes
names and addresses and other details normally found in a ‘directory’. Users
simply create one document that contains the information that will be the same
in each version, and then add placeholders for the information that will be
unique to each version.
6.
Headers & Footers: It’s
important to use page numbers in many types of documents. While at it, you
might want to consider adding other related features that will make your
document look consistency and professionally done. What many people don’t seem
to take advantage of is the fact that they can insert images, such as a company
logo or an image reflecting the document’s overall theme in either the header
or footer of the document.
7. Cover
Pages: Use Microsoft Word’s
available cover page templates to make your document stand out, especially when
it is printed. Click on Insert, then Cover Pages and choose from a variety of
default cover pages Microsoft Word provides. All the default cover pages allow
you to insert the date, author and title, in an existing template that is
already set up for you, simply insert the relevant text/date and edit your font
accordingly.
8.
Search & Replace: Have you
ever spelled a word or name incorrectly throughout a whole word document? The
Word Replace feature can search for all occurrences of a particular word,
phrase or set of characters and replace them with the correct or an alternative
version. You will be given the option to replace all occurrences or to move
through them individually accepting or rejecting each change. Clicking the
Replace All button will change all occurrences of the term in the entire
document or the selected area and then report the number of changes made.
Alternatively, Find Next will find the next occurrence of the term so you can
use the Replace button to replace it or the Find Next button to leave it
unaltered and select the next candidate for replacement.
9. Spell
Check: If you don’t want to bother
correcting spelling errors as you go, or you want to make certain you haven’t
missed any, you can run the full Word spell check from the Review tab, Proofing
group, Spelling and Grammar button (or press the F7 keyboard shortcut). When
using the main Spelling and Grammar dialog box, words in your document which
are not found in Word’s dictionary will be listed in the Not in Dictionary box.
Suggestions will be presented with the first suggestion pre-selected. The
options you have are similar to the right-click options available for
corrections as you type. There are two options available: the Change button to
correct one occurrence and the Change All button to replace all occurrences of
the word in the document with the same suggested replacement. Alternatively,
you can double-click the appropriate suggestion to change this occurrence. The
AutoCorrect button will add an item to the AutoCorrect list replacing the
marked word with the currently selected suggestion. Note that you can still
edit your document when the Spelling and Grammar dialog box is displayed, so if
none of the suggestions are appropriate, you can make your own correction
directly in the body of the document.
10. View
Options: It may
sound simple, but the option to change the document View is an underrated
feature for many MS Word users. You can change the way you view your
presentation using the buttons at the bottom of the application window.
Here are brief descriptions of what each view
does:
º Print
Layout shows the document as it will look like when printed.
º Full
Screen Reading devotes (nearly) the full screen to the contents of the document
and rearranges the contents to improve readability.
º Web
Layout displays the document laid out as though it were in a web browser.
º Outline
displays a view that allows you to restrict what is displayed to certain
outline levels. Large chunks of the document can be manipulated directly using
this view.
º Draft
displays the document content with minimum formatting and without graphics.
Regardless of which view type it is displayed
in, note that the vertical scrollbar can be used to move across the document.
Alternatively, you can also use the Page Up and Page Down keys or the arrow
keys to move through the document.
These features are just a few of Microsoft
Word’s user-friendly tools that can help you create a professional grade
document. Using these features will help you shine with arguably the world’s
most widely used word processor. Remember that proficiency with MS Word can be
a ticket to a job or business opportunity.
MS EXCEL;
ITS APPLICATIONS IN CURRENT SCENARIO
Excel is a Microsoft office application that is
mainly used for making calculations and mathematical works.
▬
It is a
spreadsheet application in which we can add sheets as per our requirements. In
a single sheet, it consists of rows and columns and cells, where every cell has
different address.
▬
Sum,
product, subtraction, division and many mathematical, logical functions are
available within it.
▬
Other
features include tables, charts, clip art and more.
▬
It is
basically used for payroll, accounts, mathematical, and for other business
purposes.
Excel is used widely in any financially-related
activity. The ability to create new
spreadsheets where users can define custom formulas to calculate anything from
a simple quarterly forecast to a full corporate annual report makes Excel
highly appealing. Excel is also used
widely for common information organization and tracking like a list of sales
leads, project status reports, contact lists, and invoicing. Finally, Excel is a useful tool for
scientific and statistical analysis with large data sets. Excel's statistical formulas and graphing can
help researches perform variance analysis, chi-square testing, and chart
complex data.
An Excel document is called a Workbook. A workbook always has at least one
Worksheet. Worksheets are the grid where
you can store and calculate data. You
can have many worksheets stored inside a workbook, each with a unique worksheet
name.
Worksheets are laid out in columns (vertical)
and rows (horizontal). The intersection
of any given row and column is a cell.
Cells are really where you enter any information. A cell will accept a large amount of text, or
you can enter a date, number, or formula.
Each cell can be formatted individually with distinct border, background
colour, and font colour/size/type.
Features of MS Excel:
1. Hyperlink: We can link one file to another file or
page.
2. Clip
art: We can add images and also audio and video
clips.
3. Charts: With charts, we can clearly show a
product(s) evaluation to a client. For example, you can display a chart showing
which product is selling more or less by month, week, and so forth.
4. Tables: Tables are created with different fields
(e.g. name, age, address, roll number, and so forth). You can add a table to
fill these values.
5. Functions: There are both mathematical functions (add,
subtract, divide, multiply), and logical ones (average, sum, mod, product).
6. Images
and backgrounds: You can
incorporate images and backgrounds into each sheet.
7. Macros: They are used for recording events for
future use.
8. Database: With the data feature, you can add any
database from other sources to it.
9. Sorting
and Filtering: We can
sort and/or filter our data so that anything redundant or repetitive can be
removed more easily.
10. Data
validations: This
tool can help you consolidate your data.
11. Grouping: The grouping feature helps you both to group
your data and ungroup it so that you have subtotals and so forth.
12. Page
layout: Themes, colours, sheets,
margins, size, backgrounds, breaks, print, titles, sheets height, width,
scaling, grids, headings, views, bring to front of font or back alignment, and
many more are available for you to lay out your page.
Microsoft
Excel provides a grid interface to organize nearly any type of
information. The power of Excel lies in
its flexibility to define the layout and structure of the information you want
to manage. Basic tasks require no
special training, and Excel allows you to work with text, numbers, and date
information in a relatively open and unstructured way. Nearly 30 years after its initial
introduction, Excel remains the world’s leading spreadsheet software.
MS
POWERPOINT; IMPORTANCE OF ITS APPLICATION IN BUSINESS
Microsoft PowerPoint allows users to create
virtual slide show presentations displaying text, images, shapes and videos.
Customization features for PowerPoint 2013 let users add animated effects to
the content and transitions between slides, such as fading slides in and out.
Sound clips can be inserted to play audio during presentations, and slides are
printable for use as handouts and projector transparencies. Users can edit, add
and delete slides as needed.
PowerPoint 2013 provides basic slide templates
such as schedules and diagrams and offers ready-made themes with professional
images, font groups and preselected colour schemes. Similar to other Office
software, PowerPoint has its own library of shapes and objects, and users can
create custom charts and graphs to share data with an audience. Users can also
apply different backgrounds to slides and insert their own diagrams and
pictures. The program includes basic grammar and spell-checking tools. To stay
current with changing technology, Microsoft has created versions of the 2013
program that are optimized for viewing on tablets, phones, widescreen monitors
and projection screens.
PowerPoint software was originally named
Presenter and developed for the Apple Macintosh platform. Microsoft acquired it
for $14 million in 1987 and eventually included it as part of the Office suite.
The main purpose of MS PowerPoint is to enable
the user to create dynamic, informational slide shows through the use of text,
graphics, and animation. Slide shows created with the software are often
displayed on projection screens for business, training, or educational
presentations, although they can be distributed as stand-alone files.
Additionally, the slides can be arranged and printed as handouts for reference.
PowerPoint is a complete presentation graphics
package. It gives you everything you need to produce a professional-looking
presentation. PowerPoint offers word processing, outlining, drawing, graphing,
and presentation management tools- all designed to be easy to use and learn.
The following gives you a quick overview of
what you can do in PowerPoint:
▬
When you
create a presentation using PowerPoint, the presentation is made up of a series
of slides. The slides that you create using PowerPoint can also be presented as
overhead transparencies or 35mm slides.
▬
In
addition to slides, you can print audience handouts, outlines, and speaker's
notes.
▬
You can
format all the slides in a presentation using the powerful Slide Master which
will be covered in the tutorial.
▬
You can
keep your entire presentation in a single file- all your slides, speaker's
notes, and audience handouts.
▬
You can
import what you have created in other Microsoft products, such as Word and
Excel into any of your slides.
▬
PowerPoint's
headline feature collects slides of text into a slideshow used for
presentations and public speaking. A good PowerPoint presentation uses images
and colors to illustrate the points of the speech.
▬
PowerPoint
can also play presentations on its own without an active speaker. Set up
PowerPoint on an unattended computer at an event by setting transition times in
advance.
▬
You
don't even need a copy of PowerPoint on a computer to play back a recorded
presentation if you save the file as a video.
▬
PowerPoint
has built-in animation tools for moving objects on the screen during a
presentation. Though often used simply as a stylish touch for text,
PowerPoint's animations also work to create stand-alone animations when saved
as a video.
DATABASE; DATABASE MANAGEMENT
SYSTEM; ITS APPLICATIONS
Database is a collection of related data and data is a
collection of facts and figures that can be processed to produce information.
Mostly data represents recordable facts.
Data aids in producing information, which is based on facts. For example, if we
have data about marks obtained by all students, we can then conclude about
toppers and average marks.
A database
can be termed as a repository of data. A collection of actual data which
constitutes the information regarding an organisation is stored in a database.
For e.g., there are 1000 students in a college & we have to store their
personal details, marks details etc., these details will be recorded in a
database.
A collection of programs that enables
you to store, modify, and extract information from a database is known as Data Base
Management System (DBMS). The primary goal of a DBMS is to provide a way to
store & retrieve database information that is both convenient &
efficient.
A database management system stores data
in such a way that it becomes easier to retrieve, manipulate, and produce
information.
Database systems are designed to manage
large bodies of information. Management of data involves both defining
structures for storage of information & providing way for manipulation of
data. In addition, the database system must ensure safety of data.
Users of DBMS
A typical DBMS has
users with different rights and permissions who use it for different purposes.
Some users retrieve data and some back it up. The users of a DBMS can be broadly
categorized as follows:
▫ Administrators- Administrators maintain the DBMS and are
responsible for administrating the database. They are responsible to look after
its usage and by whom it should be used. They create access profiles for users
and apply limitations to maintain isolation and force security. Administrators
also look after DBMS resources like system license, required tools, and other
software and hardware related maintenance.
▫ Designers- Designers are the group of people who
actually work on the designing part of the database. They keep a close watch on
what data should be kept and in what format. They identify and design the whole
set of entities, relations, constraints, and views.
▫ End Users- End users are those who actually reap the
benefits of having a DBMS. End users can range from simple viewers who pay
attention to the logs or market rates to sophisticated users such as business
analysts.
Database
System Applications:
There
are many different types of DBMSs, ranging from small systems that run on
personal computers to huge systems that run on mainframes. Databases are
applied in wide no. of applications. Following are some of the examples:-
▫ Banking: For
customer information, accounts, loans & other banking transactions
▫ Airlines: For
reservation & schedule information
▫ Universities: For
student information, course registration, grades etc.
▫ Credit card transaction: For purchase of credit cards &
generation of monthly statements.
▫ Telecommunication: For keeping records of calls made, generating monthly bill etc.
▫ Finance: For
storing information about holdings, sales & purchase of financial
statements
▫ Sales: For
customer, product & purchase information
▫ Manufacturing: For management of supply chain.
▫ Human Resource: For recording information about employees, salaries, tax, benefits etc.
We
can say that whenever we need to have a computerized system, we need a database
system.
CHARACTERISTICS OF A DBMS;
PURPOSE OF A DBMS
Characteristics of DBMS
Traditionally, data
was organized in file formats. DBMS was a new concept then, and all the
research was done to make it overcome the deficiencies in traditional style of
data management. A modern DBMS has the following characteristics:
▫ Real-world entity- A
modern DBMS is more realistic and uses real-world entities to design its
architecture. It uses the behaviour and attributes too. For example, a school
database may use students as an entity and their age as an attribute.
▫ Relation-based tables- DBMS
allows entities and relations among them to form tables. A user can understand
the architecture of a database just by looking at the table names.
▫ Isolation of data and
application- A database system is entirely
different than its data. A database is an active entity, whereas data is said
to be passive, on which the database works and organizes. DBMS also stores
metadata, which is data about data, to ease its own process.
▫ Less redundancy- DBMS follows the rules of normalization,
which splits a relation when any of its attributes is having redundancy in
values. Normalization is a mathematically rich and scientific process that
reduces data redundancy.
▫ Consistency- Consistency is a state where every relation
in a database remains consistent. There exist methods and techniques, which can
detect attempt of leaving database in inconsistent state. A DBMS can provide
greater consistency as compared to earlier forms of data storing applications
like file-processing systems.
▫ Query Language- DBMS is equipped with query language, which
makes it more efficient to retrieve and manipulate data. A user can apply as
many and as different filtering options as required to retrieve a set of data.
Traditionally it was not possible where file-processing system was used.
▫ ACID Properties- DBMS follows the concepts of Atomicity,
Consistency, Isolation, and Durability (normally
shortened as ACID). These concepts are applied on transactions, which
manipulate data in a database. ACID properties help the database stay healthy
in multi-transactional environments and in case of failure.
▫ Multiuser and
Concurrent Access- DBMS supports multi-user
environment and allows them to access and manipulate data in parallel. Though
there are restrictions on transactions when users attempt to handle the same
data item, but users are always unaware of them.
▫ Multiple views- DBMS offers multiple views for different
users. A user who is in the Sales department will have a different view of
database than a person working in the Production department. This feature
enables the users to have a concentrate view of the database according to their
requirements.
▫ Security- Features like multiple views offer security
to some extent where users are unable to access data of other users and
departments. DBMS offers methods to impose constraints while entering data into
the database and retrieving the same at a later stage. DBMS offers many
different levels of security features, which enables multiple users to have
different views with different features. For example, a user in the Sales
department cannot see the data that belongs to the Purchase department.
Additionally, it can also be managed how much data of the Sales department
should be displayed to the user. Since a DBMS is not saved on the disk as
traditional file systems, it is very hard for miscreants to break the code.
Purpose
of Database system
A
file system is one in which we keep the information in operating system files.
Before the evolution of DBMS, organisations used to store information in file
systems. A typical file processing system is supported by a conventional
operating system. The system stores permanent records in various files & it
need application program to extract records, or to add or delete records.
We
will compare both systems with the help of an example.
There
is a saving bank enterprise that keeps information about all customers &
saving accounts. Following manipulations has to be done with the system
▫ A program to
debit or credit an account
▫ A program to add
a new account.
▫ A program to
find balance of an account.
▫ A program to
generate monthly statements.
As
the need arises new applications can be added at a particular point of time as
checking accounts can be added in a saving account. Using file system for
storing data has got following disadvantages:
1. Data Redundancy & Inconsistency
Different programmers
work on a single project so various files are created by different programmers
at some interval of time. So various files are created in different formats
& different programs are written in different programming language.
Same information is
repeated. For ex name & address may appear in saving account file as well
as in checking account. This redundancy results in higher storage space &
access cost. It also leads to data inconsistency which means that if we change
some record in one place the change will not be reflected in all the places.
For ex. a changed customer address may be reflected in saving record but not
anywhere else.
2. Difficulty in Accessing data
Accessing data from a
list is also a difficulty in file system. Suppose we want to see the records of
all customers who has a balance less than $10,000, we can either check the list
& find the names manually or write an application program .If we write an
application program & at some later time, we need to see the records of customer
who have a balance of less than $20,000, then again a new program has to be
written.
It means that file
processing system do not allow data to be accessed in a convenient manner.
3. Integrity Problems
Sometimes, we need that
data stored should satisfy certain constraints as in a bank a minimum deposit
should be of $100. Developers enforce these constraints by writing appropriate
programs but if later on some new constraint has to be added then it is
difficult to change the programs to enforce them.
4. Atomicity Problems
Any mechanical or
electrical device is subject to failure, and so is the computer system. In this
case we have to ensure that data should be restored to a consistent state. For
example an amount of $50 has to be transferred from Account A to Account B. Let
the amount has been debited from account A but have not been credited to
Account B and in the mean time, some failure occurred. So, it will lead to an
inconsistent state.
So, we have to adopt a
mechanism which ensures that either full transaction should be executed or no
transaction should be executed i.e. the fund transfer should be atomic.
5. Security Problems
All the user of
database should not be able to access all the data, e. g., a payroll. Personnel
needs to access only that part of data which has information about various
employees & are not needed to access information about customer accounts.
DATA DICTIONARY; TYPES OF
DATA DICTIONARY
A
data dictionary can be defined as a DBMS component that stores the definition
of data characteristics and relationships. We may call it “data about data”
which, in other words, is known as metadata.
The DBMS data dictionary provides the DBMS with its self describing
characteristic. In effect, the data dictionary resembles and X-ray of the
company’s entire data set, and is a crucial element in the data administration
function.
The
two main types of data dictionary exist, integrated
and stand alone. An integrated data dictionary is included
with the DBMS. For example, all relational DBMSs include a built in data
dictionary or system catalogue that is frequently accessed and updated by the
RDBMS. Other DBMSs especially older types, do not have a built in data
dictionary instead the DBA (Database
Administrator) may use third party stand
alone data dictionary systems.
Data
dictionaries can also be classified as active
or passive. An active data dictionary is automatically updated by the DBMS with
every database access, thereby keeping its access information up-to-date. A passive data dictionary is not updated
automatically and usually requires a batch process to be run. Data dictionary
access information is normally used by the DBMS for query optimization purpose.
The
data dictionary’s main function is to store the description of all objects that
interact with the database. Integrated data dictionaries tend to limit their
metadata (“data about data”) to the
data managed by the DBMS. Stand alone data dictionary systems are more usually
more flexible and allow the DBA to describe and manage all the organization’s
data, whether or not they are computerized. Whatever the data dictionary’s
format, its existence provides database designers and end users with a much
improved ability to communicate. In addition, the data dictionary is the tool
that helps the DBA to resolve data conflicts.
Although,
there is no standard format for the information stored in the data dictionary
several features are common. For example, the data dictionary typically stores
descriptions of all:
▫ Data elements that are define in
all tables of all databases. Specifically the data dictionary stores the name,
data-types, display formats, internal storage formats, and validation rules.
The data dictionary tells where an element is used, by whom it is used and so
on.
▫ Tables define in all databases. For
example, the data dictionary is likely to store the name of the table creator,
the date of creation access authorizations, the number of columns, and so on.
▫ Indexes define for each database
tables. For each index the DBMS stores at least the index name the attributes
used, the location, specific index characteristics and the creation date.
▫ Define databases: who created each
database, the date of creation where the database is located, who the DBA is
and so on.
▫ End users and The Administrators of
the data base.
▫ Programs that access the database
including screen formats, report formats application formats, SQL (Structured Query Language) queries and
so on.
▫ Access authorization for all users
of all databases.
▫ Relationships among data elements
which elements are involved: whether the relationship is mandatory or optional,
the connectivity and cardinality and so on.
Data
dictionary/directory subsystem keeps track of the definitions of all the data
items in the database. This includes elementary-level data items (fields),
group and record-level data structures and relational tables. It keeps track of
relationships that exist between various data structures. It maintains the
indexes that are used to access data quickly. It also keeps track of screen and
report format definitions that may be used by various application programs.
The
metadata stored in the data dictionary is often the basis for monitoring the
database use and assignment of access rights to the database users. The
information stored in the database is usually based on the relational table
format, thus, enabling the DBA to query the database with SQL (Structured Query Language) command. For
example, SQL command can be used to extract information about the users of the
specific table or about the access rights of a particular user.
DATA MODELS; TYPES OF DATA
MODELS
Data
models define how the logical structure of a database is modeled. Data Models
are fundamental entities in a DBMS. Data models define how data is connected to
each other and how they are processed and stored inside the system.
In
other words, data models are a
collection of conceptual tools for describing data, data relationships, data
semantics and data constraints.
There are various kinds of data
models i.e. in a database records can be arranged in various ways. The various
ways in which data can be represented are:-
1. Hierarchical data model
2. Network data model
3. Relational Model
4. E-R-Model
THE HIERARCHICAL MODEL
Organization of the records is as a
collection of trees. As its name implies, the Hierarchical Database Model
defines hierarchically-arranged data.
Perhaps the most intuitive way to
visualize this type of relationship is by visualizing an upside down tree of
data. In this tree, a single table acts as the "root" of the database
from which other tables "branch" out.
Relationships in such a system are thought of in
terms of children and parents such that a child may only have one parent but a
parent can have multiple children. Parents and children are tied together by
links called "pointers" (perhaps physical addresses inside the file
system). A parent will have a list of pointers to each of their children.
If we want to create a structure where in a course various
students are there & these students are given certain marks in assignment.
NETWORK DATABASES
In many ways, the
Network Database model was designed to solve some of the more serious problems
with the Hierarchical Database Model. Specifically, the Network model solves
the problem of data redundancy by representing relationships in terms of sets
rather than hierarchy.
The network model is
very similar to the hierarchical model actually. In fact, the hierarchical
model is a subset of the network model. However, instead of using a
single-parent tree hierarchy, the network model uses set theory to provide a
tree-like hierarchy with the exception that child tables were allowed to have
more than one parent. This allowed the network model to support many-to-many
relationships.
Thus, children can have
multiple parents and parents can have multiple children.
RELATIONAL MODEL
Relational
data model is the primary data model, which is used widely around the world for
data storage and processing. This model is simple and it has all the properties
and capabilities required to process data with storage efficiency.
Concepts
Tables-
In relational data model, relations are
saved in the format of Tables. This format stores the relation among entities.
A table has rows and columns, where rows represent records and columns
represent the attributes.
Tuple-
A single row of a table, which contains a
single record for that relation, is called a tuple.
Relation instance-
A finite set of tuples in the relational
database system represents relation instance. Relation instances do not have
duplicate tuples.
Relation schema-
A relation schema describes the relation
name (table name), attributes, and their names.
Relation key-
Each row has one or more attributes,
known as relation key, which can identify the row in the relation (table)
uniquely.
Attribute domain-
Every attribute has some pre-defined
value scope, known as attribute domain.
Constraints
Every
relation has some conditions that must hold for it to be a valid relation.
These conditions are called Relational Integrity Constraints. There are three
main integrity constraints −
▫ Key
constraints
▫ Domain
constraints
▫ Referential
integrity constraints
Key Constraints: There
must be at least one minimal subset of attributes in the relation, which can
identify a tuple uniquely. This minimal subset of attributes is called key for
that relation. If there is more than one such minimal subset, these are called
candidate keys.
Key
constraints force that -
▫ In
a relation with a key attribute, no two tuples can have identical values for
key attributes.
▫ A
key attribute cannot have NULL values.
Key
constraints are also referred to as Entity
Constraints.
Domain Constraints: Attributes
have specific values in real-world scenario. For example, age can only be a
positive integer. The same constraints have been tried to employ on the
attributes of a relation. Every attribute is bound to have a specific range of
values. For example, age cannot be less than zero and telephone numbers cannot
contain a digit outside 0-9.
Referential integrity
Constraints: Referential integrity constraints work
on the concept of Foreign Keys. A foreign key is a key attribute of a relation
that can be referred in other relation.
Referential
integrity constraint states that if a relation refers to a key attribute of a
different or same relation, then that key element must exist.
E-R MODEL
ER considers the real
world to consist of entities and relationships among them. An entity is a
`thing' which can be distinctly identified, for example a person, a car, a
subroutine, a wire, an event.
A ‘Relationship’ is an association among entities, e.g. person ‘Owns’ car is an association between a
person and a car person ‘Eats’ dish ‘In’ place is an association among a
person, a dish and a place.
The information about
one entity is expressed by a set of attribute.
NETWORKING;
ITS FEATURES AND IMPORTANCE
The term ‘‘computer network’’ means
a collection of autonomous computers interconnected by a single technology. Two
computers are said to be interconnected if they are able to exchange
information. The connection need not be via a copper wire; fibre optics,
microwaves, infrared, and communication satellites can also be used. Networks
come in many sizes, shapes and forms, as we will see later. They are usually
connected together to make larger networks, with the Internet being the most
well-known example of a network of networks.
Computer networking is the practice
of interfacing two or more computing devices with each other for the purpose of
sharing data. Computer networks are built with a combination of hardware and
software.
A Computer Network is a connection
of two or more Computers through a medium for exchanging information or data
communication. It is also called as Data Network where you can easily send and
receive data to or from a Computing device. These computing devices may be
PC’s, Workstations, and Mainframes that are connected to Printers, modems,
CD/DVD ROM and other peripherals for sharing resources over a network. The
connections of the Computers over a Network are possible through several
networking devices like routers, bridges, gateways, cables, Satellites and
others. Internet is the best example of Computer network that helps you to
exchange data between two or more Computers over a network. But Computer
Network main function is to provide a medium for connecting and linking to
various computing devices for easy data communication.
Computer networks are very useful
in many ways for communication over a network through email or chat rooms,
sharing Hardware resources for printing or scanning a document, sharing files
and data on a storage device, sharing software applications and run remotely on
other computers and many more.
Features
of Computer Network
1.
Sharing
Resources from one Computer to another Computer over a network
2.
Performance
by measuring the speed of data transmission with number of users, connectivity
and the software used
3.
Reliability
makes easy to use an alternative source for data communication in case of
hardware failure or connectivity issues
4.
Scalability
increases the system performance by adding more processors
5.
Security
is the main characteristics of Computer network where you can take necessary
steps for protecting your data from unauthorized access
6.
Create
files and store them in one computer, access those files from the other
computer(s) connected over the network
7.
Connect
a printer, scanner, or a fax machine to one computer within the network and let
other computers of the network use the machines available over network.
Importance
of Computer Network
Computer networks have highly benefited
various fields of educational sectors, business world and many organizations.
They can be seen everywhere they connect people all over the world. There are
some major advantages which computer networks have provided making the human
life more relaxed and easy. Some of them are listed below:
1.
Communication:
Communication is one of the biggest
advantages provided by the computer networks. Different computer networking
technologies have improved the way of communication. People from the same or
different organizations can communicate in a matter of minutes for
collaborating for the work activities. In offices and organizations computer
networks are serving as the backbone of the daily communication from top to
bottom level of organization. Different types of software can be installed
which are useful for transmitting messages and emails at fast speed.
2.
Data
sharing: Another
wonderful advantage of computer networks is data sharing. All the data such as
documents, files, accounts information, reports, multi-media, etc., can be
shared with the help computer networks. Hardware sharing and application
sharing is also allowed in many organizations such as banks and small firms.
3.
Instant
and multiple accesses: Computer networks are multiply processed where many users can access
the same information at the same time. Immediate commands such as printing
commands can be made with the help of computer networks.
4.
Video
conferencing: Before
the arrival of the computer networks there was no concept for video
conferencing. LAN and WAN have made it possible for the organizations and
business sector to use the live video conferencing for important discussions
and meetings.
5.
Internet
Service: Computer
networks provide internet service over the entire network. Every single
computer attached to the network can experience the high speed internet. Fast
processing and work load distribution.
6.
Broadcasting:
With the help of computer networks news
and important messages can be broadcasted just in a matter of seconds which
saves a lot of time and effort.
7.
Photographs
and large files:
Computer network can also be used for sending large data files such as high
resolution photographs over the computer network to more than one user at a
time.
8.
Cost
Saver: Computer
networks are important as they help in saving a lot of cost for any
organization in different ways. Networking helps in building up links between
different people which further helps in sharing files and messages with these
people which reduces transportation and communication expense. It also raises
the standard of the organization because of the advanced technologies that are used
in networking.
9.
Remote
access and login:
Employees of different or same organization connected by the networks can
access the networks by simply entering the network remote IP or web remote IP.
In this the communication gap which was present before the computer networks no
more exist.
10.
Flexible:
Computer networks are quite flexible. All
of its topologies and networking strategies support addition for extra components
and terminals to the network. They are equally fit for large as well as small
organizations.
11.
Reliable:
Computer networks are reliable when
safety of the data is concerned. If one of the attached systems collapses same
data can be gathered from another system attached to the same network.
12.
Data
transmission:
Data is transferred at a fast speed even in the scenarios when one or two
terminals machine fails to work properly. Transmission of data is seldom
affected in computer networks. Almost
complete communication can be achieved in critical scenarios too.
TYPES
AND TOPOLOGIES OF COMPUTER NETWORKS
Types
of computer networks
Personal
Area Networks:
A PAN (Personal Area Network) lets devices communicate over the range of a
person. A common example is a wireless network that connects a computer with
its peripherals. Almost every computer has an attached monitor, keyboard,
mouse, and printer. Without using wireless, this connection must be done with
cables. So many new users have a hard time finding the right cables and
plugging them into the right little holes (even though they are usually colour
coded) that most computer vendors offer the option of sending a technician to
the user’s home to do it. To help these users, some companies got together to
design a short-range wireless network called Bluetooth to connect these
components without wires. The idea is that if your devices have Bluetooth, then
you need no cables. You just put them down, turn them on, and they work
together. For many people, this ease of operation is a big plus.
Local
Area Networks: The
next step up is the LAN (Local Area Network). A LAN is a privately owned
network that operates within and nearby a single building like a home, office
or factory. LANs are widely used to connect personal computers and consumer
electronics to let them share resources (e.g., printers) and exchange
information. When LANs are used by companies, they are called enterprise
networks. Wireless LANs are very popular these days, especially in homes, older
office buildings, cafeterias, and other places where it is too much trouble to
install cables. In these systems, every computer has a radio modem and an
antenna that it uses to communicate with other computers.
Metropolitan
Area Network: A
MAN (Metropolitan Area Network) covers a city. The best-known examples of MANs
are the cable television networks available in many cities. These systems grew
from earlier community antenna systems used in areas with poor over-the-air
television reception. In those early systems, a large antenna was placed on top
of a nearby hill and a signal was then piped to the subscribers’ houses.
Wide
Area Network: A
WAN (Wide Area Network) is a network that exists over a large-scale
geographical area. A WAN connects different smaller networks, including local
area networks (LAN) and metropolitan area networks (MAN). This ensures that
computers and users in one location can communicate with computers and users in
other locations. WAN implementation can be done either with the help of the
public transmission system or a private network. A WAN connects more than one
LAN and is used for larger geographical areas. WANs are similar to a banking
system, where hundreds of branches in different cities are connected with each
other in order to share their official data.
Types
of Network Topology
Network Topology is the schematic
description of a network arrangement, connecting various nodes (sender and
receiver) through lines of connection.
Features of Bus
Topology
▬
It transmits data only
in one direction.
▬
Every
device is connected to a single cable
RING
Topology: It
is called ring topology because it forms a ring as each computer is connected
to another computer, with the last one connected to the first. Exactly two
neighbours for each device.
Features of Ring
Topology
▬
A
number of repeaters are used for Ring topology with large number of nodes,
because if someone wants to send some data to the last node in the ring
topology with 100 nodes, then the data will have to pass through 99 nodes to
reach the 100th node. Hence to prevent data loss repeaters are used in the
network.
▬
The
transmission is unidirectional, but it can be made bidirectional by having 2
connections between each Network Node, it is called Dual Ring Topology.
▬
In
Dual Ring Topology, two ring networks are formed, and data flow is in opposite
direction in them. Also, if one ring fails, the second ring can act as a
backup, to keep the network up.
▬
Data is transferred in
a sequential manner that is bit by bit. Data transmitted, has to pass through
each node of the network, till the destination node.
STAR
Topology: In
this type of topology all the computers are connected to a single hub through a
cable. This hub is the central node and all others nodes are connected to the
central node.
Features of Star
Topology
▬
Every
node has its own dedicated connection to the hub.
▬
Hub
acts as a repeater for data flow.
▬
Can
be used with twisted pair, Optical Fibre or coaxial cable.
Features of Mesh
Topology
▬
Fully connected.
▬
Robust.
▬
Not
flexible.
TREE
Topology: It
has a root node and all other nodes are connected to it forming a hierarchy. It
is also called hierarchical topology. It should at least have three levels to the
hierarchy.
▬
Ideal
if workstations are located in groups.
▬
Used
in Wide Area Network.
HYBRID
Topology: It
is two different types of topologies which is a mixture of two or more
topologies. For example if in an office in one department ring topology is used
and in another star topology is used, connecting these topologies will result
in Hybrid Topology (ring topology and star topology).
Features of Hybrid
Topology
▬
It
is a combination of two or topologies.
▬
Inherits
the advantages and disadvantages of the topologies included.
INTERNET; THE USAGE OF
INTERNET TO SOCIETY
The Internet is a worldwide,
publicly accessible network of networks. Through interconnected computer
networks, the Internet enables individuals and businesses to share information,
resources, and services. A collection of interconnected networks is called an
internetwork or internet. The Internet (also known as the Net) is a worldwide
network of computers. Today people use the Internet for everything from
electronic mail to shopping, from learning to entertainment. This network of
computers is called the Internet. This worldwide information highway is
comprised of thousands of interconnected computer networks, and reaches
millions of people in many different countries. The Internet was originally
developed for the United States military, and then became used for government,
academic and commercial research and communications. It is now available to
anyone with a PC, ISP, modem and browser.
The Internet is a global system of
interconnected computer networks that use the standard Internet Protocol Suite
(TCP/IP) to serve billions of users worldwide. It is a network of networks that
consists of millions of private, public, academic, business, and government
networks, of local to global scope, that are linked by a broad array of
electronic and optical networking technologies. The Internet carries a vast
range of information resources and services, such as the inter-linked hypertext
documents of the World Wide Web (WWW) and the infrastructure to support
electronic mail.
Uses
of Internet
1.
Large
volume of Information: Internet can be used to collect information from around the world. This
information could relate to education, medicine, literature, software,
computers, business, entertainment, friendship, tourism, and leisure. People
can search for information by visiting the home page of various search engines
such as Google, Yahoo, Bing, etc.
2.
News
and Journals:
All the newspapers, magazines and journals of the world are available on the
Internet. With the introduction of broadband and advanced mobile
telecommunication technologies such as 3G (third generation) and 4G (fourth
generation), the speed of internet service has increased tremendously. A person
can get the latest news about the world in a matter of few seconds.
3.
Electronic
Mode of Communication: Internet has given the most exciting mode of communication to all. We
can send an E-mail (the short form of Electronic Mailing System) to all the
corners of the world.
4.
Chatting:
There are many chatting software that can
be used to send and receive real-time messages over the internet. We can chat
with our friend and relatives using any one of the chatting software.
5.
Social
Networking: People
can connect with old friends on social networking sites. They can even chat
with them when they are online. Social networking sites also allow us to share
pictures with others. We can share pictures with our loved ones, while we are
on a vacation. People are even concluding business deals over these social
networking sites such as Facebook.
6.
Online
Banking (Net-Banking): The use of internet can also be seen in the field of banking
transactions. Many banks such as HSBC, SBI, Axis Bank, HDFC Bank, etc. offers
online banking facilities to its customers. They can transfer funds from one
account to another using the net-banking facility.
7.
E-commerce:
Internet is also used for carrying out
business operations and that set of operations is known as Electronic Commerce
(E-commerce). Flipkart is the largest e-commerce company in India. The rival,
Amazon, is giving stiff competition to Flipkart.
8.
Mobile
commerce: Mobile
commerce (also M-Commerce) refers to the commercial transaction that takes
place over the mobile internet. Using the mobile internet technology, many
companies have introduced mobile version of websites and mobile apps, to
promote and sell their products. Customers can simply browse several through
the products and buy online through mobile internet.
9.
Mobile
wallet: Many
companies offer the service of mobile wallet to its customers. Users must have
a smart-phone and internet connection to use this service. Users can pay an
amount into their mobile wallet, which they can use to make online payment such
as bill payments, recharges, etc.
10.
Entertainment:
Apart from a major source of knowledge
and information, the utility of Internet in the field of entertainment cannot
be undermined. We can visit various video sites and watch movies and serials at
our convenient time.
11.
Technology
of the Future: Internet
is the technology of future. In the times to come, offices would be managed at
distant places through Internet.
INTERNET PROTOCOLS
When two humans converse, they
may have to use the same language but they generally understand each other
without having to adhere to rigid rules of grammar or formal language
frameworks. Computers, on the other hand, have to have everything explicitly
defined and structured. If computers wish to communicate with one another, they
have to know in advance exactly how information is to be exchanged and
precisely what the format will be. Therefore, standard methods of transmitting
and processing various kinds of information are used and these methods are
called "protocols". Protocols are established by international
agreement and ensure that computers everywhere can talk to one another. There
are a variety of protocols for different kinds of information and functions.
TCP/IP
TCP (Transmission Control Protocol) and IP (Internet Protocol) are two different procedures that are often
linked together. The linking of several protocols is common since the functions
of different protocols can be complementary so that together they carry out
some complete task. The combination of several protocols to carry out a
particular task is often called a "stack" because it has layers of
operations. In fact, the term "TCP/IP" is normally used to refer to a
whole suite of protocols, each with different functions. This suite of
protocols is what carries out the basic operations of the Web. TCP/IP is also
used on many local area networks.
When information is sent over the
Internet, it is generally broken up into smaller pieces or "packets".
The use of packets facilitates speedy transmission since different parts of a
message can be sent by different routes and then reassembled at the
destination. It is also a safety measure to minimize the chances of losing
information in the transmission process. Transmission
Control Protocol (TCP) is the means for creating the packets, putting them
back together in the correct order at the end, and checking to make sure that
no packets got lost in transmission. If necessary, TCP will request that a
packet be resent.
Internet
Protocol (IP)
is the method used to route information to the proper address. Every computer
on the Internet has to have its own unique address known as the IP address.
Every packet sent will contain an IP address showing where it is supposed to
go. A packet may go through a number of computer routers before arriving at its
final destination and IP controls the process of getting everything to the
designated computer. Note that IP does not make physical connections between
computers but relies on TCP for this function. IP is also used in conjunction
with other protocols that create connections.
FTP
File
Transfer Protocol
(FTP) lives up to its name and provides a method for copying files over a
network from one computer to another. More generally, it provides for some
simple file management on the contents of a remote computer. It is an old
protocol and is used less than it was before the World Wide Web came along.
Today, Its primary use is uploading files to a Web site. It can also be used
for downloading from the Web but, more often than not, downloading is done via
HTTP. Sites that have a lot of downloading (software sites, for example) will
often have an FTP server to handle the traffic. If FTP is involved, the URL
will have ftp: at the front.
The Internet is a heterogeneous
worldwide network consisting of a large number of host computers and local area
networks. The Internet uses the TCP/IP suite of protocols. This allows the
integration of a large number of different computers into one single network
with highly efficient communication between them. This way, the user can access
information on all kinds of host computers from a desktop PC, Macintosh, or
whatever he/she have available.
HTTP
The
Hypertext Transfer Protocol (HTTP) is an application-level protocol for
distributed, collaborative, hypermedia information systems. HTTP has been in
use by the World-Wide Web global information initiative since 1990. The first
version of HTTP, referred to as HTTP/0.9, was a simple protocol for raw data
transfer across the Internet. HTTP/1.0, as defined by RFC* 1945 [6], improved the protocol by allowing messages to be in
the format of MIME-like messages, containing meta-information about the data
transferred and modifiers on the request/response semantics. However, HTTP/1.0
does not sufficiently take into consideration the effects of hierarchical
proxies, caching, the need for persistent connections, or virtual hosts. In
addition, the proliferation of incompletely-implemented applications known as
"HTTP/1.0" has necessitated a protocol version change in order for
two communicating applications to determine each other's true capabilities.
The HyperText Transfer Protocol
defines how messages are formatted and transmitted, and what actions Web
servers and browsers should take in response to various commands. For example,
when you enter a URL in your browser, this actually sends an HTTP command to
the Web server directing it to fetch and transmit the requested Web page.
HTTP is designed to permit
intermediate network elements to improve or enable communications between
clients and servers. HTTP functions as a request-response protocol in the
client-server computing model. A web browser, for example, may be the client
and an application running on a computer hosting a web site may be the server.
The client submits an HTTP request message to the server. The server which
provides resources, such as HTML files and other content, or performs other
functions on behalf of the client returns a response message to the client. The
response contains completion status information about the request and may also
contain requested content in its message body.
The other main standard that
controls how the World Wide Web works is HTML
(HyperText Markup Language: it is the main markup language for creating
web pages and other information that can be displayed in a web browser),
which covers how Web pages are formatted and displayed.
HTTP is called a stateless protocol because each
command is executed independently, without any knowledge of the commands that
came before it. This is the main reason that it is difficult to implement Web
sites that react intelligently to user input. This shortcoming of HTTP is being
addressed in a number of new technologies, including ActiveX, Java, JavaScript
and cookies.
*Request for Comments-A
Request for Comments (RFC) is a formal document from the Internet Engineering Task Force (IETF) that is the result of committee
drafting and subsequent review by interested parties.
The Secure Socket Layer (SSL) and
Transport Layer Security (TLS) is the most widely deployed security protocol
used today. It is essentially a protocol that provides a secure channel between
two machines operating over the Internet or an internal network. In today’s
Internet focused world, the SSL protocol is typically used when a web browser
needs to securely connect to a web server over the inherently insecure
Internet.
Technically, SSL is a transparent
protocol which requires little interaction from the end user when establishing
a secure session. In the case of a browser for instance, users are alerted to
the presence of SSL when the browser displays a padlock, or, in the case of
Extended Validation SSL, when the address bar displays both a padlock and a
green bar. This is the key to the success of SSL – it is an incredibly simple
experience for end users.
As opposed to unsecured HTTP URLs
which begin with "http://" and use port 80 by default, secure HTTPS
URLs begin with "https://" and use port 443 by default.
Extended Validation (EV) SSL
Certificates (such as GlobalSign ExtendedSSL) display visible trust indicators:
Standard SSL Certificates (such
as GlobalSign DomainSSL and OrganizationSSL) display:
HTTP is insecure and is subject
to eavesdropping attacks which, if critical information like credit card
details and account logins is transmitted and picked up, can let attackers gain
access to online accounts and sensitive information. Ensuring data is either
sent or posted through the browser using HTTPS is ensuring that such
information is encrypted and secure.
In
practice, how is SSL used in today’s modern e-commerce enabled / online
workflow and service society?
§ To secure online credit card transactions.
§ To secure system logins and any sensitive
information exchanged online.
§ To secure webmail and applications like Outlook Web
Access, Exchange and Office Communications Server.
§ To secure workflow and virtualisation applications
like Citrix Delivery Platforms or cloud-based computing platforms.
§ To secure the connection between an email client
such as Microsoft Outlook and an email server such as Microsoft Exchange.
§ To secure the transfer of files over https and
FTP(s) services such as website owners updating new pages to their websites or
transferring large files.
§ To secure hosting control panel logins and activity
like Parallels, cPanel, and others.
§ To secure intranet based traffic such as internal
networks, file sharing, extranets, and database connections.
§ To secure network logins and other network traffic
with SSL VPNs such as VPN Access Servers or applications like the Citrix Access
Gateway.
All
these applications have a number of shared themes:
§ The data being transmitted over the Internet or
network needs confidentiality. In other words, people do not want their credit
card number, account login, passwords or personal information to be exposed
over the Internet.
§ The data needs to remain integral, which means that
once credit card details and the amount to be charged to the credit card have
been sent, a hacker sitting in the middle cannot change the amount to be
charged and where the funds should go.
§ Your organisation needs identity assurance to
authenticate itself to customers / extranet users and ensure them they are
dealing with the right organisation.
§ Your organisation needs to comply with regional,
national or international regulations on data privacy, security and integrity.
WORLD WIDE WEB; BASIC INTERNET TERMINOLOGY
World Wide Web is a
hypermedia-based system for browsing Internet sites. It is named the web
because it is made of many sites linked together; users can travel from one
site to another by clicking on hyperlinks. Text, graphics, sound, and video can
all be accessed with browsers like Internet Explorer, Netscape, Chrome or
Firefox.
Tim Berners-Lee, who developed
the original web model, came up with a simple language that lets somebody
developing a web document embed pointers to related resources. When you then
call up that document, you’ll see some words in a different colour or otherwise
highlighted. By moving your cursor to one of those words and then hitting enter
(or clicking on it with your mouse, depending on your interface) you will call
up the linked document.
These hyperlinks are easy to
create so anybody can put together a web resource that can become a central
clearing house of information on virtually any topic, linking documents that
could be physically stored in dozens of locations around the world. The
language that Tim Berners-Lee developed is a version of the markup language,
SGML (Standardised General Markup Language), which he called HTML (HyperText
Markup Language).
Basic
Internet Terminology
▫ ARPANET: The acronym stands for Advanced
Research Projects Agency Network. ARPA of the United States Department of
Defense developed ARPANET, which became the world's first packet switching
network. Internet is the successor of ARPANET.
▫ Internet Service Provider: A company,
which provides users with access to the Internet, is known as an Internet
service provider or Internet access provider. ISP, as it is called, offers
email accounts and other services like remote storage of files, to its
customers.
▫ IP Address: It is a way of numerically identifying
an entity on a computer network. The original addressing system known as IPv4,
used 32 bit addresses. With the growth of the Internet, IPv6 came to be used
wherein the addresses are composed of 128 bits.
▫ Cyberspace: This term coined by William Gibson, is
used to refer to computer networks connected to each other and the content they
host. It is often used to refer to the Internet.
▫ WWW: It is a collection of interlinked
documents that are accessible over the Internet. It consists of millions of web
pages that contain text, images, voice, and videos. Sir Tim Berners-Lee, a
British scientist working at CERN, created the World Wide Web.
▫ W3C: It is the acronym used for the World
Wide Web Consortium, which develops standards for the web community.
▫ Website: A website is a set of web pages
consisting of text, audio, and video. Web servers host websites.
▫ Web Page: Web pages are resources of information.
They are generally created in the HTML format and provide the web users with
navigational abilities through hyperlinks to other pages on the web.
▫ Home Page: The term home page is used to refer to
the page that is the default page of any website. It is the main page of a
complex website.
▫ Web Browser: A web browser is a software application
that facilitates user interaction with the text, audio, video and other
information that is located on the web.
▫ Session: It is an exchange of information
between a computer and its user. It is established for a certain period of time
after which it ends.
▫ Hyperlink: A reference in a document to another
section of the document or to another document is termed as a hyperlink.
Hyperlinks are used to redirect the user from one section of a page content to
another.
▫ Internet security: It is one of the major concerns
today. As the Internet acts as a communication platform that can be accessed by
millions of users around the world, it becomes necessary that proper security
measures be implemented. Issues like Internet safety that deal with the content
that is made accessible over the Internet are equally important. Internet
privacy refers to safeguarding the privacy of web users and of the sensitive
information on the web from hackers and stalkers.
▫ Email: It is a store-and-forward method of
writing, sending, and receiving written messages. Electronic mail is an
Internet e-mail system that uses network-based protocols to exchange messages
between network subsystems.
▫ Spamming: The act of sending unsolicited bulk
messages over an email system is known as spamming. It is an undesirable use of
the electronic messaging systems.
▫ Phishing: It is a fraudulent activity of
acquiring sensitive information by the use of a fake identity during electronic
communication. It is implemented by means of emails and instant messages
wherein a user is lured to enter his/her details, which are actually captured
by a fraudulent website.
▫ Hacking: The act of programmatically gaining
access to a computer application that is, otherwise, inaccessible. The act of
gaining unauthorized access to a computer is known as hacking. Hacking of
passwords that leads to breach of email privacy is a threat to communication
over the Internet. Internet crime refers to all the criminal activities that
are carried over the Internet.
▫ Social Networking: Social networking is about building
online communities of like-minded people. Serving as an excellent platform for
sharing of information, social networking is a rage today.
▫ Modem: It is a device that modulates analog
carrier signals to encode digital information and demodulates carrier signals
to decode information. A cable modem provides access to data signals sent over
the cable television infrastructure. Modems are commonly used for facilitating
Internet access.
▫ Blogs: Blogs are the expressions of common
masses about social or political issues or simply anything. Blogs can be in the
form of creative write-ups by writers in different parts of the world.
▫ Internet Forums: It is a bulletin board that
serves as a platform for group discussion. Registered users are free to
contribute to the issues raised in forums thus making them open discussion
platforms.
▫ Internet Search Engine: It is an
information retrieval system that is designed to help find information over the
Internet. Search engines use algorithms to scan the huge information base of
the Internet and sort it making it retrievable for the web users.
▫ Virtual Private Network: It is a private
network that allows the exchange of information between computers over a shared
or a public network.
▫ Wireless Networking: It refers to
computer networking that is carried out over the wireless media.
▫ Broadband Internet: Broadband
connectivity to the Internet provides the users with a high-speed Internet
access.
▫ Dial-up Internet: In this type of access to the
Internet, the user's computer is attached to a modem connected to a telephone
line. Dial-up Internet access involves a modem that dials into an Internet
service provider to establish a connection.
INFORMATION; EMPHASIS
ON DELIVERY OF TIMELY INFORMATION
Information is organised or
classified data which has some meaningful values for the receiver. Information
is the processed data on which decisions and actions are based.
When using information for
business purposes and storing information in an information system it is of
vital importance that the information is good and helps you make the correct
business decision. The characteristics of good information are as follows:
valid, reliable, timely, fit-for-purpose, accessible, cost-effective,
sufficiently accurate, relevant, and understandable by the user. These are
explained in more detail below:
Valid: Valid information is information is
information that is correct and can be used for the purpose that it is needed.
An example of valid is information that you can trust such as information
supplied to you by a governing body. Valid financial information would be tax
rates supplied to companies from the Governments Tax Office.
Reliable: Reliable information if information that you
can rely on as being correct. It will be from a valid and trusted source. An
example of reliable information would be information from your sales department
that is supplied to the financial department on the sales figures for last
month. As this comes from an internal information source it is reliable and can
be trusted.
Timely: Timely is another important characteristic
of good information. Information should be available when required. Timely
information is information that is from the correct time period. If a company
wants to analyse current profit and loss then they will need to access current
sales figures and not the sales figures from 10 years ago. We can also say that
timely information is information that is available as and when needed. For
example if a Manager needed to check the sales figures for today timely information
would be information that they could print from a cash register immediately at
any time during the day.
Fit
for Purpose:
Information that is fit for purpose means
that it is relevant to what you need it for. For example if you were opening a
business in London then it would be advisable to look at the population within
a certain area beside where you wanted to open the business. Looking at
information about the population of Papua New Guinea would not really be fit
for purpose in this instance.
Accessible: Accessible information is information that
is stored in a way that it can be easily accessed at any time. If we refer back
to the example of looking at sales figures on a cash register at any time of
the day having the feature of printing out current sales from the cash register
means that the information is accessible. If it took one hour to process the
sales figures and print them then this information would not be easily
accessible. Accessible is an important characteristic of good information as users
need to have information available to them as and when they need it.
Cost
Effective:
Cost effective information is information
that is worth investing the time and money to get to help make business
decisions. As an example, if you paid a company to do a survey for you and it
cost `1000 and you were then able to use the information
supplied to increase your profits by `1500
in the next month then this could be seen as cost effective information.
However, if the survey cost `50000 to
complete and the information only seen a `100
increase in sales in the next month them this information would not be seen as
cost effective. Cost effective information is information that costs a lot less
to put together than the resultant profit from analyzing and using the information
to increase profits.
Sufficiently Accurate: Accurate information helps businesses make the correct decisions. If
the speedometer in your car was out by 20 kmph then this information may result
in you breaking the law. Similarly if a sales department sent inaccurate sales
figures to the finance department this might result in incorrect tax
calculations for the company that would put them in danger.
Relevant: Relevant information is information that is
directly related to your business need. If a business was looking to cut costs
they might look at their electricity bill and try to see where they could save
money. If a bakery was looking at the price of metal then this would not really
be relevant information to their business. Relevant information for a bakery
would be looking at the price of ingredients to use in their products.
Understandable
by the user:
Information that is used for a business
purpose needs to be understandable by the end user. If a non financial person
wanted information about the sales for the last 3 years and you presented them
with a complex set of figures taken from a database with no clear totals then
they would not understand it. However, if you knew exactly what they wanted you
might present them with an easy to read graph with clear instructions on the
totals sales for each of the last 3 years.
INFORMATION
SYSTEM; NEED FOR AN EFFICIENT INFORMATION SYSTEM
Many organizations work with
large amounts of data. Data are basic values or facts and are organized in a
database. Many people think of data as synonymous with information; however,
information actually consists of data that has been organized to help answers
questions and to solve problems. An information system is defined as the
software that helps organize and analyze data. So, the purpose of an
information system is to turn raw data into useful information that can be used
for decision making in an organization.
Components of
Information Systems
While information systems may
differ in how they are used within an organization, they typically contain the
following components:
▬ Hardware:
Computer-based information systems use computer hardware, such as processors,
monitors, keyboard and printers.
▬ Software:
These are the programs used to organize, process and analyze data.
▬ Databases:
Information systems work with data, organized into tables and files.
▬ Network:
different elements need to be connected to each other, especially if many
different people in an organization use the same information system.
▬ Procedures:
These describe how specific data are processed and analyzed in order to get the
answers for which the information system is designed.
Importance of
Information Systems in an Organization
Information systems gain their
importance by processing the data from company inputs to generate information
that is useful for managing your operations. To increase the information
system's effectiveness, you can either add more data to make the information
more accurate or use the information in new ways.
Communication: Part of management is gathering and
distributing information, and information systems can make this process more
efficient by allowing managers to communicate rapidly. Email is quick and
effective, but managers can use information systems even more efficiently by
storing documents in folders that they share with the employees who need the
information. This type of communication lets employees collaborate in a
systematic way. Each employee can communicate additional information by making
changes that the system tracks. The manager collects the inputs and sends the
newly revised document to his target audience.
Operations:
Managing a company's operations depend
on the information available with the company. Information systems can offer
more complete and more recent information, allowing you to operate your company
more efficiently. You can use information systems to gain a cost advantage over
competitors or to differentiate yourself by offering better customer service.
Sales data give you insights about what customers are buying and let you stock
or produce items that are selling well. With guidance from the information
system, you can streamline your operations.
Decisions:
The company information system can help
you make better decisions by delivering all the information you need and by
modelling the results of your decisions. A decision involves choosing a course
of action from several alternatives and carrying out the corresponding tasks.
When you have accurate, up-to-date information, you can make the choice with
confidence. If more than one choice looks appealing, you can use the
information system to run different scenarios. For each possibility, the system
can calculate key indicators such as sales, costs and profits to help you
determine which alternative gives the most beneficial result.
Records:
Your Company needs records of its
activities for financial and regulatory purposes as well as for finding the
causes of problems and taking corrective action. The information system stores
documents and revision histories, communication records and operational data.
The trick to exploiting this recording capability is organizing the data and
using the system to process and present it as useful historical information.
You can use such information to prepare cost estimates and forecasts and to
analyze how your actions affected the key company indicators.
TYPES OF
INFORMATION SYSTEM
Understanding the various levels
of an organization is essential to understand the information required by the
users who operate at their respective levels.
The following diagram illustrates
the various levels of a typical organization.
Operational
Management Level:
The operational level is concerned with performing day to day business
transactions of the organization.
Examples of users at this level
of management include cashiers at a point of sale, bank tellers, nurses in a
hospital, customer care staff, etc.
Users at this level make
structured decisions. This means that they have defined rules that guide them
while making decisions.
For example, if a store sells
items on credit and they have a credit policy that has some set limit on the
borrowing. All the sales person needs to decide whether to give credit to a
customer or not. There decision is based on the current credit information from
the system.
Tactical
Management Level:
This organization level is dominated by middle-level managers, heads of
departments, supervisors, etc. The users at this level usually oversee the
activities of the users at the operational management level.
Tactical users make semi-structured
decisions. The decisions are partly based on set guidelines and judgmental
calls. As an example, a tactical manager can check the credit limit and
payments history of a customer and decide to make an exception to raise the
credit limit for a particular customer. The decision is partly structured in
the sense that the tactical manager has to use existing information to identify
a payments history that benefits the organization and an allowed increase
percentage.
Strategic
Management Level:
This is the most senior level in an organization. The users at this level make
unstructured decisions. Senior level managers are concerned with the long-term
planning of the organization. They use information from tactical managers and
external data to guide them when making unstructured decisions.
Information
System
A combination of hardware,
software, infrastructure and trained personnel organized to facilitate
planning, control, coordination, and decision making in an organization.
It is a discipline covering the
application of people, technologies and procedures collectively called
information systems, to solving business problems.
Academically, the term is
commonly used to refer to the group of information management methods tied to
the automation or support of human decision making.
An
information system is a software system to capture, transmit, store, retrieve,
manipulate, or display information, thereby supporting people, organizations,
or other software systems.
Types
of Information System
Transaction
Processing System (TPS): Transaction processing systems are used to record
day to day business transactions of the organization. They are used by users at
the operational management level. The main objective of a transaction
processing system is to answer routine questions such as;
º
How printers
were sold today?
º
How much
inventory do we have at hand?
º
What is the
outstanding due for John Doe?
By recording the day to day
business transactions, TPS system provides answers to the above questions in a
timely manner. The decisions made by operational managers are routine and
highly structured. The information produced from the transaction processing
system is very detailed.
For example, banks that give out
loans require that the company that a person works for should have a Memorandum
of Understanding (MoU) with the bank. If a person whose employer has a MoU with
the bank applies for a loan, all that the operational staff has to do is verify
the submitted documents. If they meet the requirements, then the loan application
documents are processed. If they do not meet the requirements, then the client
is advised to see tactical management staff to see the possibility of signing a
MoU.
Examples
of transaction processing systems include;
▬
Point of Sale Systems – records daily sales
▬
Payroll systems –
processing employees’ salary, loans management, etc.
▬
Stock Control systems – keeping track of inventory levels
▬
Airline booking systems – flights booking management
Management
Information System (MIS): Management Information Systems (MIS) are used by
tactical managers to monitor the organization's current performance status. The
output from a transaction processing system is used as input to a management
information system. The MIS system analyzes the input with routine algorithms
i.e. aggregate, compare and summarizes the results to produced reports that
tactical managers use to monitor, control and predict future performance.
For example, input from a point
of sale system can be used to analyze trends of products that are performing
well and those that are not performing well. This information can be used to
make future inventory orders i.e. increasing orders for well-performing
products and reduce the orders of products that are not performing well.
Examples
of management information systems include;
▬
Sales management systems – they get input from the point of sale system
▬
Budgeting systems –
gives an overview of how much money is spent within the organization for the
short and long terms.
▬
Human resource management system – overall welfare of the employees, staff turnover,
etc.
Tactical managers are responsible
for the semi-structured decision. MIS systems provide the information needed to
make the structured decision and based on the experience of the tactical
managers, they make judgement calls i.e. predict how much of goods or inventory
should be ordered for the second quarter based on the sales of the first
quarter.
Decision
Support System (DSS): Decision support systems are used by senior
management to make non-routine decisions. Decision support systems use input
from internal systems (transaction processing systems and management
information systems) and external systems.
The main objective of decision
support systems is to provide solutions to problems that are unique and change
frequently. Decision support systems answer questions such as;
º
What would be
the impact of employees' performance if we double the production lot at the
factory?
º
What would
happen to our sales if a new competitor entered the market?
Decision support systems use
sophisticated mathematical models, and statistical techniques (probability,
predictive modelling, etc.) to provide solutions, and they are very
interactive.
Examples
of decision support systems include;
▬
Financial planning systems – it enables managers to evaluate alternative ways
of achieving goals. The objective is to find the optimal way of achieving the
goal. For example, the net profit for a business is calculated using the
formula Total Sales less (Cost of Goods + Expenses). A financial planning
system will enable senior executives to ask what if questions and adjust the
values for total sales, the cost of goods, etc. to see the effect of the
decision and on the net profit and find the most optimal way.
▬
Bank loan management systems – it is used to verify the credit of the loan
applicant and predict the likelihood of the loan being recovered.
Artificial
intelligence techniques in business: Artificial intelligence systems mimic
human expertise to identify patterns in large data sets. To identify data that
is most relevant to you, companies such as Amazon, Facebook, and Google, etc.
use artificial intelligence techniques.
Let's use Facebook as an example, Facebook usually makes very accurate
predictions of people that you might know or went with to school. They use the
data that you provide to them, the data that your friends provide and based on
this information make predictions of people that you might know.
Amazon uses artificial
intelligence techniques too to suggest products that you should buy also based
on what you are currently getting.
Google also uses
artificial intelligence to give you the most relevant search results based on
your interactions with Google and your location.
These techniques have greatly
contributed in making these companies very successful because they are able to
provide value to their customers.
Online
Analytical Processing (OLAP): Online
analytical processing
(OLAP) is used to query and analyze multi-dimensional data and produce
information that can be viewed in different ways using multiple dimensions.
Let's say a company sells
laptops, desktops, and mobile device. They have four (4) branches A, B, C and
D. OLAP can be used to view the total sales of each product in all regions and
compare the actual sales with the projected sales.
Each piece of information such as
product, number of sales, sales value represents a different dimension. The
main objective of OLAP systems is to provide answers to ad hoc queries within
the shortest possible time regardless of the size of the datasets being used.
INFORMATION
TECHNOLOGY; ITS ROLE IN TODAY’S SOCIETY
The term “information” has a
diversity of meanings, from everyday usage to technical interpretations.
Generally speaking, the concept of information is associated with knowledge
derived from study, experience, or instruction. Technology, on the other hand,
refers to the application of knowledge to the practical aims of human life, or
to changing and manipulating the human environment. Technology includes the use
of materials, tools, techniques and sources of power to make life easier or
more pleasant and work more productive. Technology began to influence human
endeavour as soon as people began using tools. Technology also started being
used for managing information when the amount and variety of information grew
to such vast proportions that the human brain could neither store nor process
it efficiently.
Definition:
The
term Information Technology (IT) was coined by Jim Domsic of Michigan in
November 1981. Domsic created the term to modernize the outdated phrase
"data processing". Information Technology is a general term that
describes any technology that helps to produce, manipulate, store, communicate
and/or disseminate information. Presumably, when speaking of Information
Technology as a whole, it is noted that the use of computers and information
are associated. “Information Technology” as defined by the Information
Technology Association of America (ITAA), is "the study, design,
development, implementation, support or management of computer-based
information systems, particularly software applications and computer
hardware." IT deals with the use of computers and computer software to
convert, store, protect, process, transmit and securely retrieve information.
Encompassing the computer and
information systems industries, Information Technology is the capability to
electronically input, process, store, output, transmit, and receive data and
information, including text, graphics, sound, and video, as well as the ability
to control machines of all kinds electronically. Information Technology is
comprised of computers, networks, satellite communications, robotics, video,
text, cable television, electronic mail ("e-mail"), electronic games,
and automated office equipment. The information industry consists of all
computer, communications, and electronics-related organizations, including
hardware, software, and services. Completing tasks, using Information
Technology, result in rapid processing and information mobility, as well as
improved reliability and integrity of processed information.
Another related term, Information
and Communications Technology (ICT) is sometimes used in preference to
Information Technology, particularly in the fields of education and governance.
In common usage, it is often assumed that ICT is synonymous with IT; ICT in
fact encompasses any medium to record information, technology for broadcasting
information; and technology for communicating through voice and/or images. It
includes the wide variety of computing hardware (PCs, servers, mainframes,
networked storage), the rapidly developing personal hardware market (mobile
phones, personal devices, MP3 players), application software (from the smallest
home-developed spreadsheet to online software services); and the hardware and
software needed to operate networks for transmission of information. Thus, ICT
makes more explicit that technologies such as broadcasting and wireless mobile
telecommunications are included.
Applications
of Information Technology
Science
and Engineering:
Scientific progress in fields like biotechnology is almost entirely dependent
on the use of computers and other microprocessor-controlled devices. Using
supercomputers, meteorologists predict future weather by using a combination of
observations of weather conditions from many sources, a mathematical
representation of the behaviour of the atmosphere, and geographic data.
Computer-aided design (CAD) and computer-aided manufacturing (CAM) programs
have led to improved products in many fields, especially where designs tend to
be very detailed. Computer programs make it possible for engineers to analyze
designs of complex structures such as power plants and space stations.
Business
& Commerce:
One of the first and largest applications of computers is keeping and managing
business and financial records. Most large companies keep the employment
records of all their workers in large databases that are managed by computer
programs. Similar programs and databases are used in business functions like
billing customers; tracking payments received and payments to be made; and
tracking supplies needed and items produced, stored, shipped, and sold. In
fact, practically all the information companies need to do business involves
the use of computers and Information Technology. Almost all the financial
transactions in the world are done electronically. Newer technologies like
m-commerce have enabled almost everybody to carry out routine financial
transactions, on the move.
On a smaller scale, many
businesses have replaced cash registers with point-of-sale (POS) terminals.
These POS terminals not only print a sales receipt for the customer but also
send information to a computer database when each item is sold to maintain an
inventory of items on hand and items to be ordered. Computers have also become
very important in modern factories. Computer-controlled robots now do tasks
that are hot, heavy, or hazardous. Robots are also used to do routine,
repetitive tasks in which boredom or fatigue can lead to poor quality work.
With today's sophisticated
hardware, software, and communications technologies, it is often difficult to
classify a system as belonging uniquely to one specific application program.
Organizations increasingly are consolidating their information needs into a single,
integrated information system. Management Information System (MIS), with the
Chief Information Officer (CIO) at its head, is a whole, new branch of
enterprise management.
Education: The advent of
Information Technology has changed the meaning of the term “literate”, with
computer literacy being almost as important as basic literacy in many cases.
Computer education is an essential course at the primary level in most schools
across the world. With more information getting digitized every day, and the internet
making it accessible to anyone across the world, students are increasingly
relying on electronic sources of information rather than physical libraries for
their needs. Instructional methodology has also undergone a sea change with use
of images, animations, videos, presentations and e-learning to complement
traditional techniques.
Governance: The concept of
e-governance is one of the most novel applications of Information Technology
whereby it is changing the lives of millions across the globe. Computerization
of Government activities makes it easier to supervise and audit, and makes the
administration more responsive to the needs of society. It also bridges the
divide between the Government and the people. Technologies like touch-screen
kiosks help disseminate information on land records, photo identity cards,
pending bills etc. and enable even illiterate people to take more informed
decisions. India is leading the world in the effective use of IT for elections.
Medicine: Information
Technology plays an important role in medicine. For example, a scanner takes a
series of pictures of the body by means of computerized axial tomography (CAT)
or magnetic resonance imaging (MRI). A computer then combines the pictures to
produce detailed three-dimensional images of the body's organs. In addition,
the MRI produces images that show changes in body chemistry and blood flow.
Most critical life support equipment are programmed to respond to changes in
the patient’s status in split-seconds, thereby reducing the response time and
risk of human error. Newer concepts like robotic surgery enable specialists to
perform surgeries from remote locations. Genomic studies greatly depend on
supercomputing power to develop technologies for the future.
Entertainment: IT has changed
the lifestyle of most people. The convergence of various technologies has
created various options for entertainment like games, streaming music and
video, digital television broadcasts, satellite radio, animated movies etc.
which can be accessed with the help of mobile phones, PDAs, notebook computers
or on television either with a cable connection or wirelessly using
newer-generation Wi-Fi, CDMA or GPRS technologies.
APPLICATIONS OF
I. T. IN VARIOUS FUNCTIONAL AREAS OF MANAGEMENT
FINANCE: Information technology focuses on the
development of electronic networks that exchange information. Because all
financial transactions involve the exchange of information, the increasing
popularity of online finance coincided with advances in information technology.
Information
technology allows finance to function on a global level. "Financial
markets can be thought of as the first organized, global information markets
operating through networked computers," Winn says. Without information
technology, financial markets couldn't react to global developments and finance
companies couldn't consistently acquire information at the same time as their
competitors. For example, the Internet allows continuous access to credit
scores and credit ratings to all lenders, insurance companies and businesses
that need financially responsible customers.
The information
technology that runs social media on the Internet provides financial
institutions with valuable information on their customers. By encouraging
online communities associated with their products, finance companies not only
acquire information but also encourage brand loyalty. For example, websites
such as ‘TradeKing’ allow online stock traders to discuss their picks and
advise newcomers. Socially driven information technology allows finance
companies to contact the younger demographics that will be their future
customers.
HOSPITALITY: With the Hospitality Industry high on
the Industry scale every hotel is now intent on gaining the maximum. Where
earlier the focus was on selling rooms the same is now shifted to maximization
of room yield. Guest room is a perishable commodity. Arriving at a potential
value of room when in demand is an art. Keeping the manual track of a bulk room
inventory, looking at the future booking trends and calculating the potential
room rate manually is too tedious a task.
This job is
eased by ‘Revenue enhancement\Yield Management’ application as systems looks
into current bookings, past history, future booking trends and various events
(repetitive and non repetitive in nature) to calculate the best possible rate
at which a guest room can be sold.
Few years ago
air travel was a luxury. Today with the application of yield management various
Airlines in India are able to offer best rates to passengers depending on the
current load and increase their PLF (Passenger load factor) creating a win-win
situation for both the Airline and the Customer. Many private Airlines have
started concept of e-ticketing and advance seat booking.
Similarly hotel
room booking and various other travel-tourism related services could be booked
by a customer on-line at the best available rate. Advance IT software and
systems make it possible for many agents and operators to provide a bouquet of
complete services- i.e. from Airline ticket booking, airport pick and drop to
Hotel room booking along with sightseeing at very nominal rates due to
consolidation and integration of all travel and tourism related services using
various software’s and booking engines interface. Due to this integration,
booking engines are empowered to great deals to customers online.
MARKETING: Information technology is an essential
partner in management of your business, regardless of the kind of enterprise
you operate. Whether you need computers for storage, transfer, retrieval or
transmission of information, you can manage your business with greater accuracy
and efficiency with the assistance of information technology and computer
applications.
Large and small
businesses are on a level playing field on the Internet. You can have a Web
presence, take orders, buy merchandise, sell excess or even operate some
businesses entirely online. A marketing tool that uses information technology
is the Quick Response or QR Code that looks like a bar code but is square. A scan
advertises your website address and includes any text you choose. You can use
your business management skills to direct employees or contractors to do your
Internet marketing, or you can choose to learn a new set of skills in
information technology.
MANUFACTURING: Computer based control systems
can be combined with manufacturing technology, such as robots, machine tools,
automated guided vehicles, to improve manufacturing operations. In this role,
the computer can assist integrating these technologies into a lean and
efficient factory capable of competing in world markets. Organizations such as
Allen-Bradley, black and Decker, and Boeing have used information technology
and factory automation to improve manufacturing operations. This combination of
information technology and factory automation is often called computer-
integrated manufacturing.
An enormous
amount of information is generated and used during the design, manufacture, and
use of a product to satisfy customer needs and to meet environmental requirements.
Thus it is reasonable to suppose that the use of information technology can
enable substantial improvements in the operation, organization, and
effectiveness of information-intensive manufacturing processes and activities,
largely by facilitating their integration. Equipment and stations within
factories, entire manufacturing enterprises, and networks of suppliers,
partners, and customers located throughout the world can be more effectively
connected and integrated through the use of information technology.
The use of
information technology in manufacturing operations can be divided into four
major groups of software systems:
a)
Enterprise
Resource Planning (ERP): ERP system
provides a firm with a common software infrastructure and database.
b)
Supply Chain
Management (SCM):
These software systems primarily focus on
how firms interact with the suppliers that are part of their overall supply
chain. Depending on where the firm is in its supply chain, this also can
involve customers.
c)
New Product
Development (NPD):
New product development software focuses
on linking the engineering function with the operations function within a firm
to facilitate the transfer of new product drawings and models into manufactured
products.
d)
Customer
Relationship Management (CRM): Customer
relationship management software, such as that provided by Siebel Systems,
focuses on the interface between the firm and its customer. In addition to
having order entry capability, these systems collect customer-specific data,
which allow the firm to provide customer-specific solutions. These software
systems are typically addressed in marketing.
HUMAN RESOURCE: Technology has changed the
business world many times over. In the Information Age, the advent of computers
and the Internet has increased that impact significantly. Many businesses
cannot even function without the use of computer technology. This impact is
seen in nearly all areas of business, including human resources, where
technology continues to have a significant impact on HR practices.
One way in which
human resources has been significantly impacted by technology is in the area of
recruiting. Before the Internet, HR recruiters had to rely on print
publications, such as newspapers, to post jobs and get prospects for open
positions. Other methods such as networking also were used, but HR recruiters
did not have the ability to post a job in one or more locations and have
millions of people see it all at once. Technology has made recruiting more
efficient and, in the hands of the right recruiter, more effective as well.
Information
technology makes it possible for human resources professionals to train new
staff members in a more efficient manner as well. The ability to access company
information and training programs from remote locations eliminates the need for
trainers to work directly with new hires on all training. Some interaction will
always be necessary on some level, of course, but training in virtual
classrooms makes it possible for the HR professionals to train a large number
of employees quickly and to assess their progress through computerized testing
programs.
Enhanced performance management
is another by-product of technological improvement. Human resources
professionals can use computer technology to assess employee performance and
also to get employee feedback to be used for the betterment of the
organization. Various software programs make it possible for human resources
professionals to examine employee performance using metrics to ensure that
employees are meeting performance standards. Employees that don't measure up
can be subjected to additional training or let go in favour a replacement that
can come in and do the job.
SOFTWARE AND ITS TYPES
Software is a set of programs,
which is designed to perform a well defined function. A program is a sequence
of instruction written to solve a particular problem.
Software is a collection of
instructions that enable the user to interact with a computer, its hardware, or
perform tasks.
Software is created
with programming languages and related utilities, which may come in several
forms: single programs like script interpreters, packages containing a
compiler, linker, and other tools; and large suites (often called Integrated
Development Environments) that include editors, debuggers, and other tools for
multiple languages.
Software can be purchased at a
retail computer store or online and come in a box containing all the disks
(floppy diskette, CD, DVD, or Blu-ray), manuals, warranty, and other
documentation.
Software can also be downloaded
to a computer over the Internet. Once downloaded, setup files are run to start
the installation process on your computer.
Free software:
There are also millions of free
software programs available that are separated into different categories:
▫ Shareware or trial software is software
that gives you a few days to try the software before you have to buy the
program. After the trial time expires, you'll be asked to enter a code or to
register the product before you can continue to use it.
▫ Freeware is completely free software that never
requires payment, as long as it is not modified.
▫ Open source software is similar to
freeware. Not only is the program given away for free, but the source code used
to make the program is as well, allowing anyone to modify the program or view
how it was created.
The first software program that
was held in electronic memory was written by Tom Kilburn. The program
calculated the highest factor of the integer 2^18 = 262,144 and was
successfully executed on June 21st of 1948 at the University of Manchester. The
computer that held that program was called the Small Scale Experimental
Machine, otherwise known as the "Baby" computer.
Types
of Software
There are two types of software:
§ System Software
§ Application
Software
Software is a generic term for
organized collections of computer data and instructions, often broken into two
major categories: system software that provides the basic non-task-specific
functions of the computer, and application software which is used by users to
accomplish specific tasks.
SYSTEM
SOFTWARE
The system software is a
collection of programs designed to operate, control, and extend the processing
capabilities of the computer itself. System software is generally prepared by
computer manufactures. These software products comprise of programs written in
low-level languages which interact with the hardware at a very basic level.
System software serves as the interface between hardware and the end users.
System software is responsible
for controlling, integrating, and managing the individual hardware components
of a computer system so that other software and the users of the system see it
as a functional unit without having to be concerned with the low-level details
such as transferring data from memory to disk, or rendering text onto a
display. Generally, system software consists of an operating system and some
fundamental utilities such as disk formatters, file managers, display managers,
text editors, user authentication (login) and management tools, and networking
and device control software.
System software is a basic
requirement for any computer, as it controls all main functions and integrates
all parts into a unitary system.
System software is a collection
of one or more programs used to control and coordinate the hardware and other
application software. Generally the system software may perform the following
functions:
§ It communicates with hardware devices.
§ It controls and monitors the proper use of various
hardware resources like CPU, memory, peripheral devices like monitor, printer
etc.
§ It supports the execution and development of other
application software.
Features of
system software are as follows:
§ Close to system
§ Fast in speed
§ Difficult to design
§ Difficult to understand
§ Less interactive
§ Smaller in size
§ Difficult to manipulate
§ Generally written in low-level language
Few examples of
system software are:
§ Operating system
§ Programming language translators
§ Communication software
§ Compiler and Interpreters
§ Command line shell
APPLICATION
SOFTWARE
Application software products are
designed to satisfy a particular need of a particular environment. All software
applications prepared in the computer lab can come under the category of
Application software.
Application software may consist
of a single program, such as a Microsoft's notepad for writing and editing
simple text. It may also consist of a collection of programs, often called a
software package, which work together to accomplish a task, such as a
spreadsheet package.
Application software may consist
of a single program, such as an image viewer; a small collection of programs
(often called a software package) that work closely together to accomplish a
task, such as a spreadsheet or text processing system; a larger collection
(often called a software suite) of related but independent programs and
packages that have a common user interface or shared data format, such as
Microsoft Office, which consists of closely integrated word processor,
spreadsheet, database, etc.; or a software system, such as a database
management system, which is a collection of fundamental programs that may
provide some service to a variety of other independent applications.
Application software is a
collection of one or more programs used to solve a specific task.
Generally software used in
banking industry, airline/railway reservation, generation of telephone or
electricity bills etc. all fall under application software.
Few examples of
application software are:
§ Word processing software
§ Spreadsheet software
§ Database software
§ Education software
§ Entertainment software
Features of
application software are as follows:
§ Close to user
§ Easy to design
§ More interactive
§ Slow in speed
§ Generally written in high-level language
§ Easy to understand
§ Easy to manipulate and use
§ Bigger in size and requires large storage space
STORAGE DEVICES; TYPES OF
STORAGE DEVICES
Storage Devices
A
storage device is any computing hardware that is used for storing, porting and
extracting data files and objects. It can hold and store information both
temporarily and permanently, and can be internal or external to a computer,
server or any similar computing device. A storage device may also be known as a
storage medium or storage media.
Storage
devices are one of the core components of any computing device. They store
virtually all the data and applications on a computer, except hardware
firmware. They are available in different form factors depending on the type of
underlying device. For example, a standard computer has multiple storage
devices including RAM, cache, a hard disk, an optical disk drive and externally
connected USB drives.
There
are two different types of storage devices:
§
Primary
storage devices: Generally smaller in size, are
designed to hold data temporarily and are internal to the computer. They have
the fastest data access speed, and include RAM and cache memory.
§
Secondary
storage devices: These usually have large storage
capacity, and they store data permanently. They can be both internal and
external to the computer, and they include the hard disk, compact disk drive
and USB storage device.
MAGNETIC
STORAGE DEVICES
Hard Drives
Hard-drives have a very
large storage capacity. They can be used to store vast amounts of data.
Hard-drives are random access devices and can be used to store all types of
films, including huge files such as movies. Data access speeds are very fast. Data
is stored inside a hard-drive on rotating metal or glass discs (called
‘platters’).
Fixed Hard Drive
A hard-drive built into
the case of a computer is known as ‘fixed’. Almost every computer has a fixed
hard-drive. Fixed hard-drives act as the main backing storage device for almost
all computers since they provide almost instant access to files (random access
and high access speeds).
Portable Hard Drive
A portable hard-drive
is one that is placed into a small case along with some electronics that allow
the hard-drive to be accessed using a USB or similar connection. Portable
hard-drives allow very large amounts of data to be transported from computer to
computer. Many portable music players (such as the iPod classic) contain tiny
hard-drives. These miniature devices are just not much bigger than a stamp, but
can still store over 100 MB of data.
Magnetic Tape
Removable
Media Magnetic Discs
A floppy disc is removable,
portable, cheap, low-capacity (1.44MB) storage medium. Floppy discs are random
access devices used for transfer small amounts of data between computers, or to
back-up small files, etc. Access times are slow. Almost every PC used to have a
floppy disc drive. These are obsolete now, having been replaced by higher
capacity technology such as CD-ROMs, DVDs and USB memory sticks.
Zip Disc
A zip disc is removable
and portable storage medium, similar in appearance to a floppy disk, but with a
much higher capacity (100MB, 250MB or 750MB). Zip discs are random access
devices which were used for data back-up or moving large files between
computers. Another obsolete storage device, zip discs were a popular
replacement for floppy discs for a few years, but they never caught on fully
before being superseded by cheaper media like CD-ROMs and CD-Rs.
Jaz Disc
A jaz disc is removable
and portable storage medium based on hard-drive technology, with a large
capacity (1GB or 2GB). Jaz discs are random access devices which were used for
data back-up or moving large files between computers. Discs were expensive to
buy and not very reliable. Like the Zip disc, this system never really caught
on and was superseded by far cheaper and more reliable and cheaper technology.
OPTICAL
STORAGE DEVICES
Read-Only
Optical Discs
CD-ROM
Compact Disc - Read-Only
Memory (CD-ROM) discs can hold around 700MB of data. The data cannot be altered
(non-volatile), so cannot be accidently deleted. CD-ROMs are random-access
devices. CD-ROMs are used to distribute all sorts of data: software (e.g.
office applications or games), music, electronic books (e.g. an encyclopaedia
with sound and video.)
DVD-ROM
Digital Versatile Disc
- Read-Only Memory (DVD-ROM) discs can hold around 4.7GB of data (a dual-layer
DVD can hold twice that). DVD-ROMs are random-access devices. DVD-ROMs are used
in the same way as CD-ROMs (see above) but, since they can hold more data, they
are also used to store high-quality video.
High
Capacity Optical Discs
Blu-Ray disks are a
recent replacement for DVDs. A Blu-Ray disc can hold25 - 50GB of data (a
dual-layer Blu-Ray disc can hold twice that). Blu-Ray discs are random-access
devices. Blu-Ray discs are used in the same way as DVD-ROMs (see above) but,
since they can hold more data, they are also used to store very high-quality,
high-definition (HD)video. The 'Blu' part of Blu-Ray refers to the fact that
the laser used to read the disc uses blue light instead of red light. Blue
light has a shorter wavelength than red light (used with CDs and DVDs). Using a
blue laser allows more data to be placed closer together on a Blu-Ray disc,
than on a DVD or CD, so Blu-Ray has a much higher storage capacity than these
older discs.
HD
DVD
Recordable
Optical Discs
Recordable optical
discs can have data written onto them (‘burnt’) by a computer user using a special
disc drive (a disc ‘burner’).
CD-R
and DVD-R
CD-Recordable (CD-R)
and DVD-recordable (DVD-R) discs can have data burnt onto them, but not erased.
You can keep adding data until the disc is full, but you cannot remove any data
or re-use a full disc. When CD-Rs and DVD-Rs are burnt, the laser makes
permanent marks on the silver-coloured metal layer. This is why these discs
cannot be erased.
CD-RW
and DVD-RW
CD-ReWritable (CD-RW)
and DVD-ReWritable (DVD-RW) discs, unlike CD-Rs and DVD-Rs, can have data burnt
onto them and also erased so that the discs can be re-used. When CD-RWs and
DVD-RWs are burnt the laser makes marks on the metal layer, but in a way that
can be undone. So these discs can be erased.
DVD-RAM
SOLID-STATE
STORAGE DEVICES
The term ‘solid-state’
essentially means ‘no moving parts’. Solid-state storage devices are based on
electronic circuits with no moving parts (no reels of tape, no spinning discs,
no laser beams, etc.) Solid-state storage devices store data using a special
type of memory called flash memory.
Flash
Memory
Flash memory is a type
of Electronically-Erasable Programmable Read-Only Memory (EEPROM). Flash memory
is non-volatile (like ROM) but the data stored in it can also be erased or
changed (like RAM). Flash memory can be found in many data storage devices.
You might wonder why,
since flash memory is non-volatile, normal computers don’t use it instead of
RAM. If they did we would have computers that you could turn off, turn back on
again and no data would be lost – it would be great. The reason is speed –
saving data to flash memory is very slow compared to saving it to RAM. If a
computer were to use flash memory as a replacement for RAM it would run very
slowly. However some portable computers are starting to use flash memory (in
the form of solid-state ‘discs’ as a replacement for hard-drives. No moving
parts mean less to go wrong and longer battery life.
Memory Cards
Many of our
digital devices (cameras, mobile phones, MP3 players, etc.) require compact,
non-volatile data storage. Flash memory cards provide this and come in a
variety of shapes and sizes.
Smart
Cards
Many credit
cards (e.g. ‘chip-and-pin’ cards), door entry cards, satellite TV cards, etc.
have replaced the very limited storage of the magnetic strip (the dark strip on
the back of older cards) with flash memory. This is more reliable and has a
much larger storage capacity. Cards with flash memory are called smart cards.












































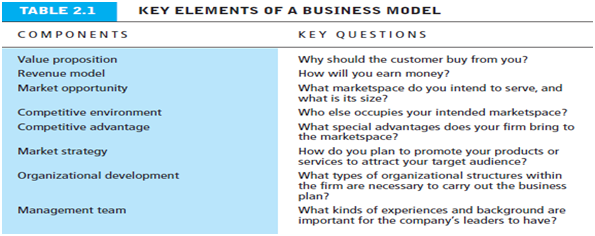
Comments
Post a Comment